Featured News
-

 327Hacked
327HackedNow Run Your Arduino Using Windows 10, Know How To Do It
A great news for Makers and Arduino lovers: Microsoft announced a new partnership with Arduino to make their Windows as First ever...
-
 270Geek
270GeekMicrosoft facial recognition tool claims it can guess your age, but does it?
Finding someone’s age and gender, no longer a problem! With Microsoft’s newest API all the age secrets are to be exposed —...
-
 298Hacked
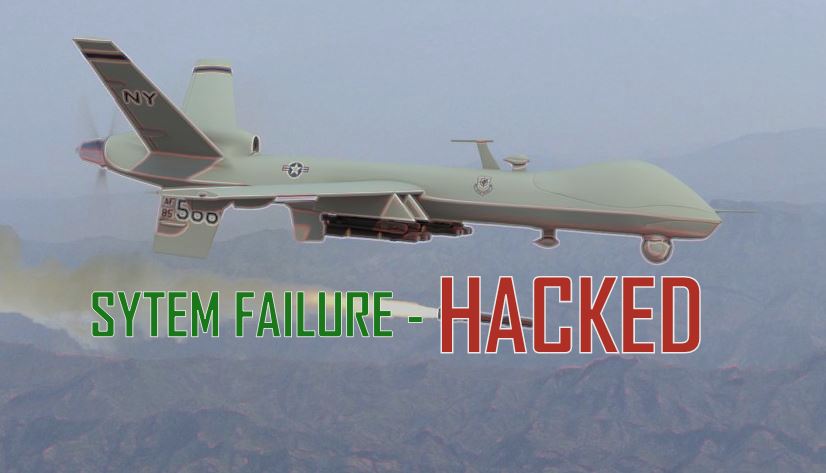
298HackedHow to Hack a Military Drone Manual is Already Online
The information needed to hack a sophisticated military drone is already available on internet and hackers could use this how-to guide for...
-

 235Surveillance
235SurveillanceACLU California Launches Police monitoring and recording app
It has been almost 25 years, but the infamous video of ‘Rodney King being beaten up by L.A. police officers’ is still...
-

 427Scams
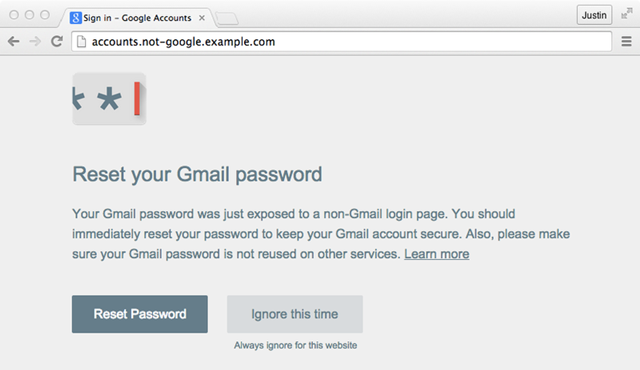
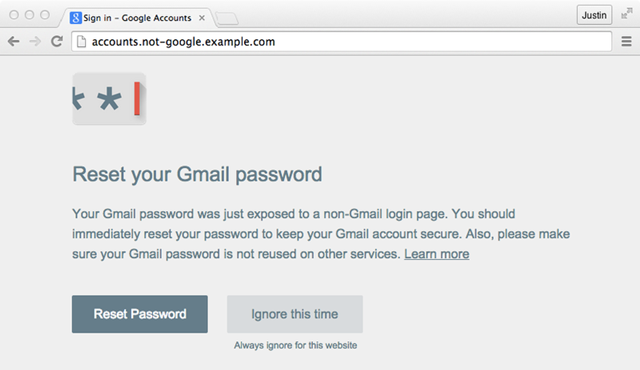
427ScamsGoogle releases Password Alert: an anti‑phishing Chrome extension
Google has taken a stand against phishing attacks by revealing Password Alert: a Chrome extension designed to neutralize them after a user...
-

 429Cyber Crime
429Cyber CrimeRyanair hack: $5 million stolen from low‑cost airline
Budget airline Ryanair has been the victim of a major banking hack, with more than $5 million stolen from its business account...
-

 64Cyber Crime
64Cyber Crime5 signs you’re in hackers’ sights
“It won’t happen to me” is often uttered by citizens and businesses who are adamant that they won’t become a victim of...
-
 280News
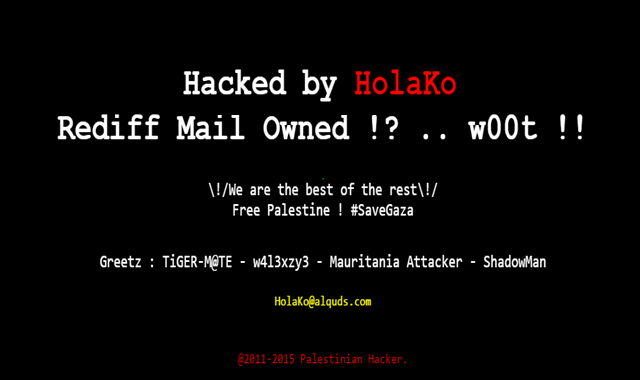
280NewsFamous online Indian portal ‘Rediff’ Hacked by Palestinian Hacker
On 30th April, 2015, a Palestinian-friendly hacker going with the online handle of HolaKo hacked and defaced a subdomain of Rediff.com, a...
-

 267Hacked
267HackedHow This Facebook Glitch Gave Me a Massive Heart Attack
It happened about two hours ago. Facebook nearly gave me and my friend Arpit, the co-founders of fossBytes, a massive heart-attack. Yes,...
-

 172Cyber Crime
172Cyber CrimeOnline Scam Alert Associated with the Nepal Earthquake Disaster
It is no secret how even the world’s most unfortunate tragedies such as air crashes, hurricanes, earthquakes and tsunamis are capitalized on...
-

 268Geek
268GeekThug arrested after liking his own ‘Mugshot Wanted’ pic on Facebook
People do dumb things on Facebook, but liking your own picture when it’s posted by the police for an arrest? Come on man! It’s...
-

 224Geek
224GeekVorlon.JS – New Open-source Framework by Microsoft For JavaScript Debugging
Microsoft is busy launching new products and services from its Developer Build Conference 2015. Yesterday we saw the unveiling of Microsoft Edge...
-
 295Hacked
295Hacked5 Most Dangerous Hackers of All Time
Do you know the difference between a “hacker” and a “cyber criminal”? Many of us often use these two terms without knowing...
-
 311Data Security
311Data SecurityNew Google Chrome extension will save you from Phishing Attacks
Google has recently unveiled a new Chrome extension called Password Alert, designed as a defense tool for phishing threats by issuing an...
-

 153Scams
153ScamsAccident Scam Waiting to Happen
Beware of that accident scam call or text: losing money isn't the only risk.
-

 208Geek
208GeekGoogle’s “Chrome Dev Browser” Now Available on Android, Get it Now
Do you want to experience all the new features of Google’s new browser for Android before everyone else? Here’s a good news....
-

 3.2KMalware
3.2KMalwareIDS, Firewall and Antivirus: what you need to have installed?
What's the difference between IDS, firewalls and antivirus? This guide should explain how they complement each other in a balanced security setup.
-

 313Hacking
313HackingHand implant chip lets hacker attack Android phones via NFC
A security expert has had a computer chip designed for tracking cows implanted into his hand by an 'unlicensed amateur' to hack...
-

 323Cyber Crime
323Cyber CrimeCanadian Woman Hacker Arrested for spying on people through webcams
A Canadian woman has been arrested by the Royal Canadian Mounted Police for hacking computers, taking over their webcams and spying on people....
-

 318Data Security
318Data SecurityFacebook Users Hit with ‘Your Facebook Login is Removed’ Malware Email
Hackers are targeting users with a fake Facebook email tricking them into clicking an attached application to generate a trusted connection to the network— Attachment contains...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




