Search results for "DDE"
-
 249Data Security
249Data SecurityDouble-click me not: Malicious proxy settings in OLE Embedded Script
Attackers have been using social engineering to avoid the increasing costs of exploitation due to the significant hardening and exploit mitigations investments...
-
 191Data Security
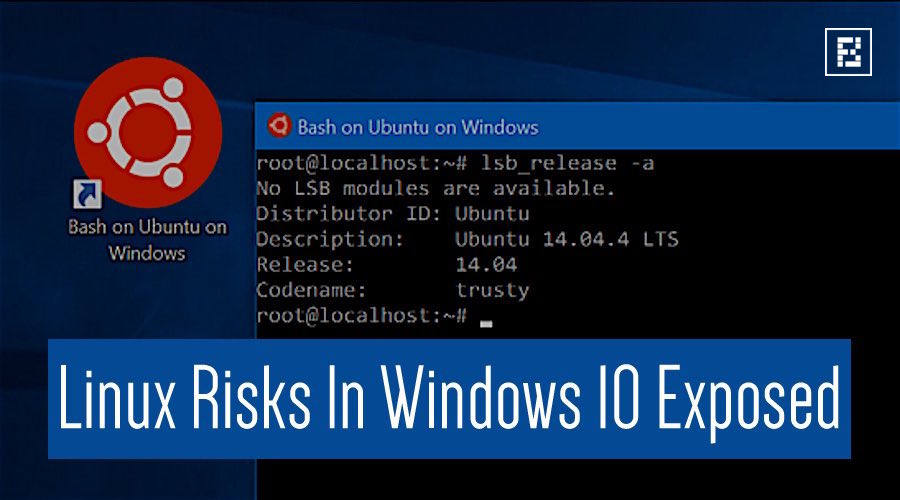
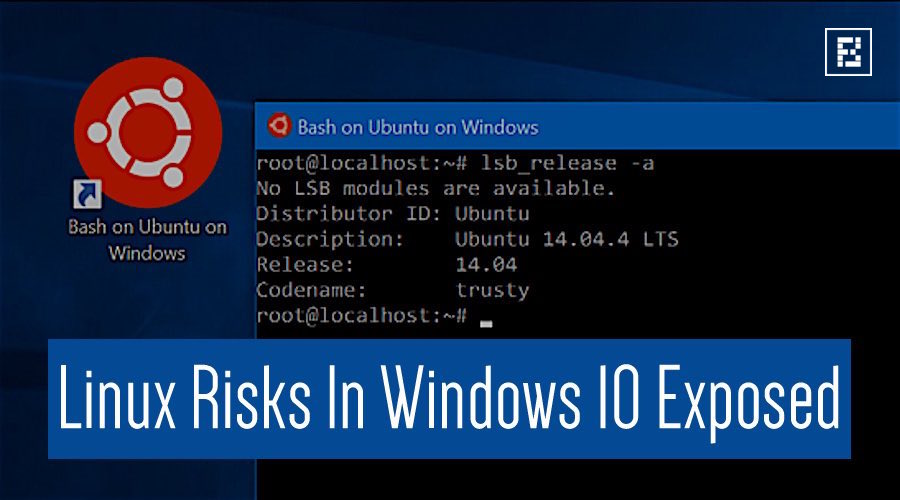
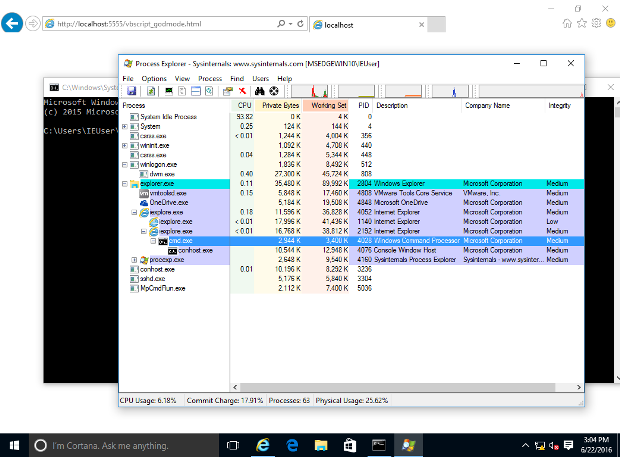
191Data SecurityRisk From Linux Kernel Hidden in Windows 10 Exposed at Black Hat
LAS VEGAS–Microsoft’s Windows 10 includes many innovative security features that are intended to help minimize risk and improve user experience. One such...
-
 201Hacked
201HackedIs Hidden Linux Subsystem In Windows 10 Making Your PC Unsafe?
Short Bytes: A security researcher has claimed that the newly-introduced Linux subsystem in Windows 10 could prove to be a risky affair by...
-
 82Vulnerabilities
82VulnerabilitiesFoolishly Open-Sourced Internet Explorer Exploit Code Added to Neutrino EK
Neutrino EK now features support for CVE-2016-0189. The crooks behind the Neutrino Exploit Kit (EK) didn’t wait long to update their automated malware...
-

 318Hacked
318HackedVoice Commands Hidden In YouTube Videos Can Hack Your Smartphone
Short Bytes: A combined research has been conducted by UC Berkeley and Georgetown University to demonstrate how distorted voice commands hidden in YouTube...
-
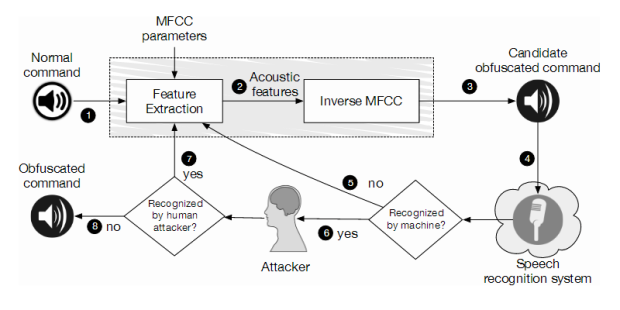
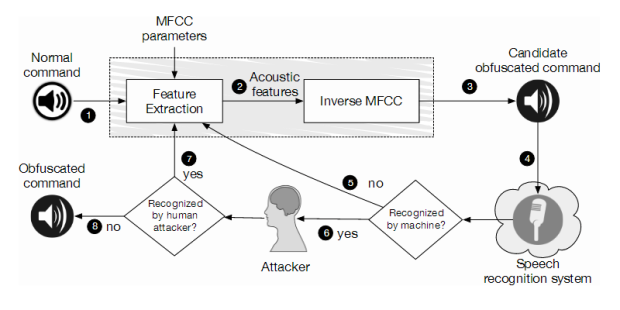 223Incidents
223IncidentsHidden Voice Commands Embedded in YouTube Videos Can Hijack Your Smartphone
Some attacks are hard to spot even by human subjects. A series of distorted voice commands surreptitiously hidden in YouTube videos can force...
-

 251How To
251How ToHow To Play Facebook Messenger’s New And Hidden Football Game
Short Bytes: Thanks to Euro 2016 season, Facebook has rolled out a new easter egg in the form of Messenger Football. All...
-
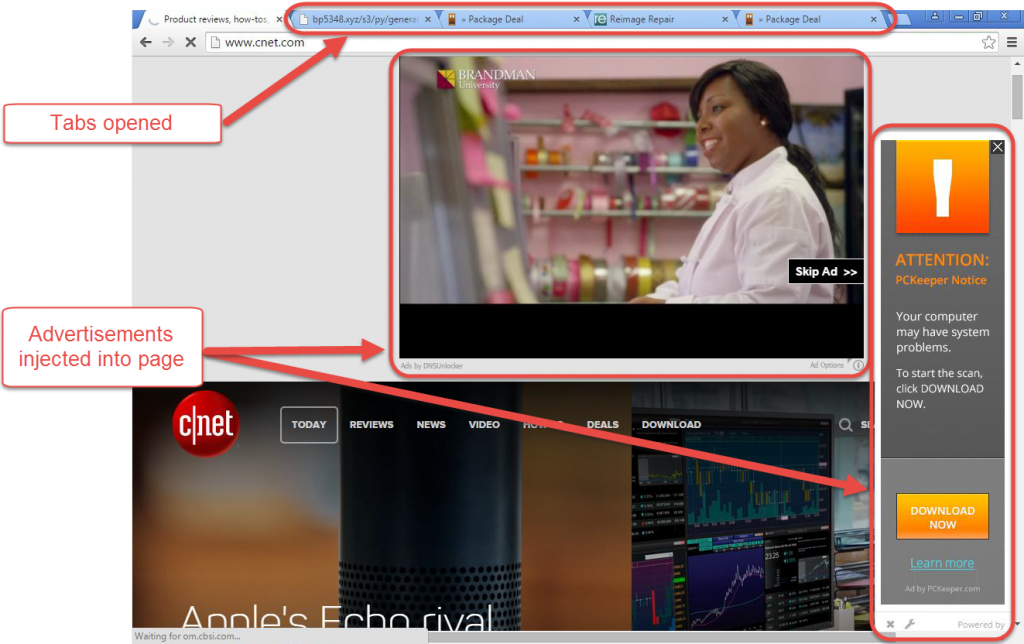
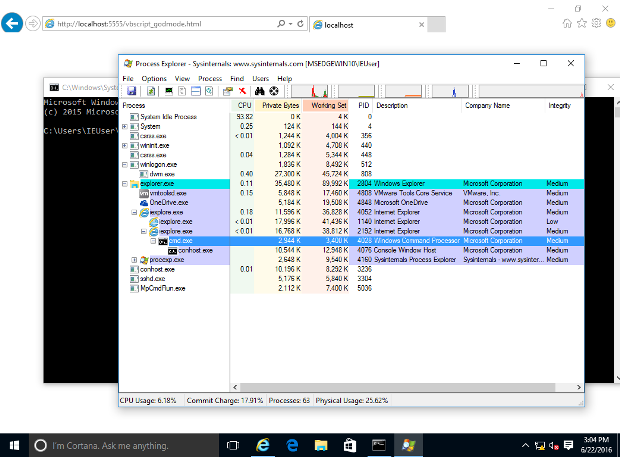
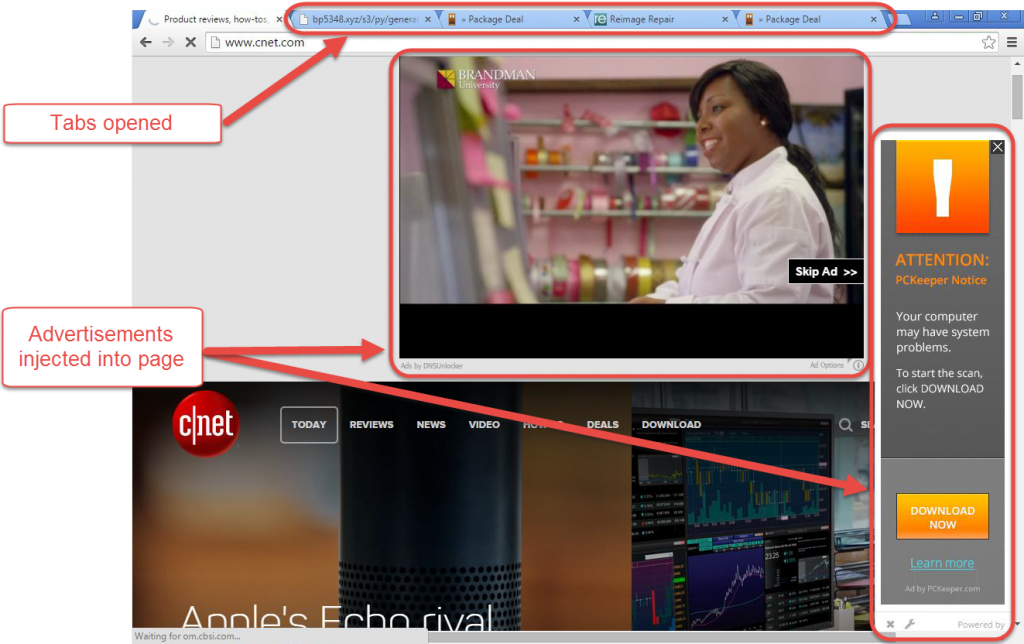 2.3KMalware
2.3KMalwareCrouching Tiger, Hidden DNS
An interesting DNS hijack that sets the victim's computer to use specific DNS servers has emerged. Here are the key details of...
-
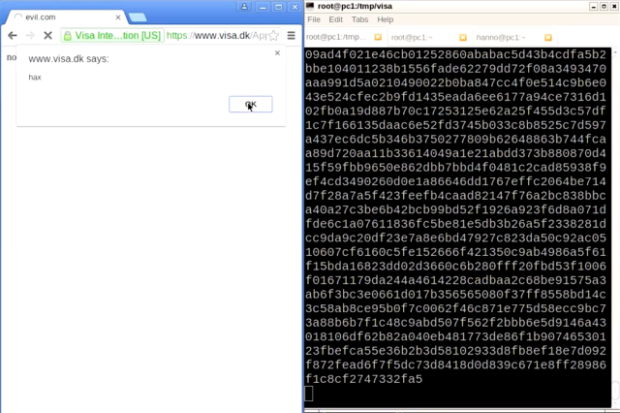
 168Data Security
168Data Security“Forbidden attack” makes dozens of HTTPS Visa sites vulnerable to tampering
Researchers say 70,000 servers belonging to others also at risk. Dozens of HTTPS-protected websites belonging to financial services giant Visa are vulnerable to...
-
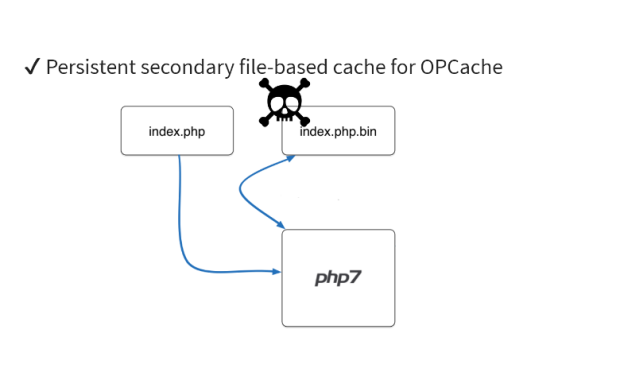
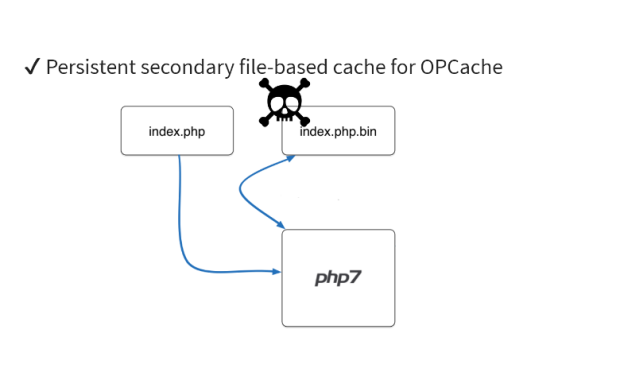 109Data Security
109Data SecurityDetecting Hidden Backdoors in PHP OPcache
In this article, we will be looking at the strategies to detect and analyze malware hidden inside an OPcache file. If you...
-

 271How To
271How ToHow To Create A Hidden User Administrator Account On Windows 10
Short Bytes: Using a hidden user administrator account on Windows 10, you can ensure the privacy of your personal data very easily....
-

 216Data Security
216Data SecurityViber adds end-to-end encryption and hidden chats as messaging app privacy wave grows
Following WhatsApp’s move to add end-to-end encryption to its platform, another big messaging company is joining the wave of apps turning on expanded privacy features.Viber...
-
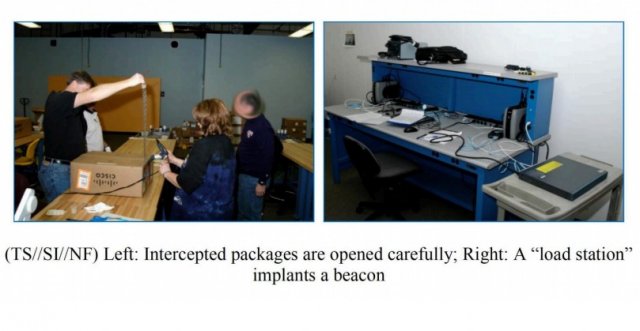
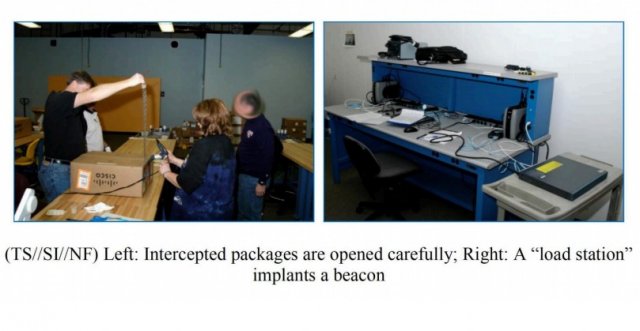 161Malware
161MalwarePhotos Show How NSA Implants Trojan In Routers For Hidden Access And Spying
ShortBytes: In a recent find out, it has been revealed how NSA implants trojan firmware in the networking devices being delivered to...
-
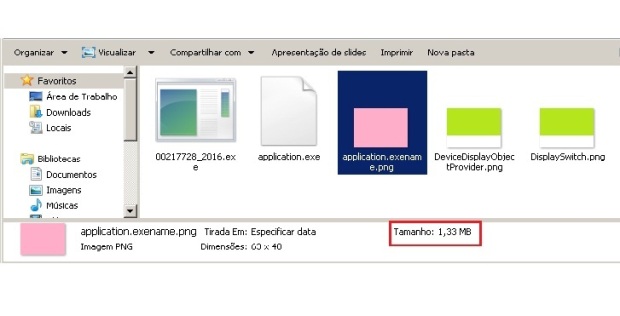
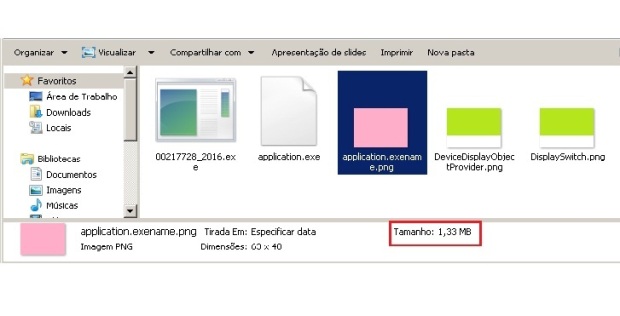 218Data Security
218Data SecurityPNG Embedded – Malicious payload hidden in a PNG file
One of the most complex tasks for the cybercriminals is to ensure their malicious code goes undetected by antivirus and achieves its...
-

 231Geek
231GeekDeveloper Survey: Java Developers Are The Saddest And C++ Programmers Are The Oldest
Short Bytes: The stereotypes associated with programmers are countless. To study them, using Microsoft’s Face API, Trestle Technology has performed a survey that...
-
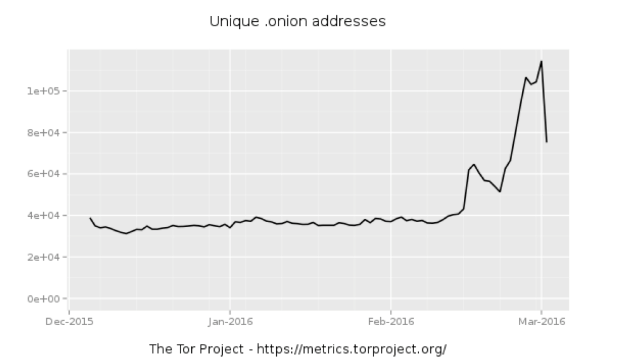
 110Data Security
110Data SecurityWhole lotta onions: Number of Tor hidden sites spikes—along with paranoia
What’s driving the surge in hidden services—is it government tampering? In recent weeks, the number of “hidden services”—usually Web servers and other Internet...
-

 178Data Security
178Data SecurityAre Hackers Keeping a Hidden Stash on Your HP Printer’s Hard Drive?
Unprotected HP printer HDDs can be abused if not protected. Security researcher Chris Vickery has discovered that HP LaserJet printers may be abused...
-
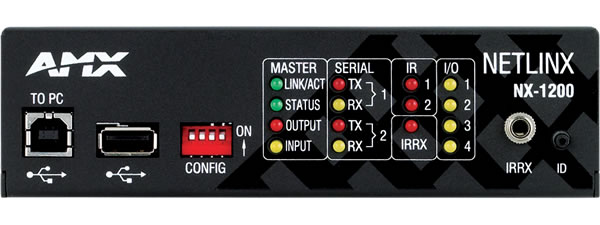
 166Incidents
166IncidentsMedia devices sold to feds have hidden backdoor with sniffing functions
Highly privileged account could be used to hack customers’ networks, researchers warn. A company that supplies audio-visual and building control equipment to...
-

 300How To
300How ToHow To Unlock Google Maps’ New Hidden Driving Mode
Short Bytes: Call it a bug or an updated feature of the Google maps, now with the updated version of Google maps,...
-

 206Tricks & How To's
206Tricks & How To'sUnlock Netflix’s hidden categories with these secret codes
Here’s a trick that’s been around for a while but may have passed you by: secret category codes added by Netflix engineers...
-

 138Data Security
138Data SecurityHow to Hack TOR Hidden Services
A lot of people think that TOR services are unhackable because they are on a “secure environment”, but the truth is that...