Search results for "DDE"
-

 246Data Security
246Data SecurityEmbedded Devices Share, Reuse Private SSH Keys, HTTPs Certificates
Researchers have found that thousands of Internet gateways, routers, modems and other embedded devices share cryptographic keys and certificates, exposing millions of...
-
 319Vulnerabilities
319VulnerabilitiesXSS in Hidden Input Fields
At PortSwigger, we regularly run pre-release builds of Burp Suite against an internal testbed of popular web applications to make sure it’s...
-
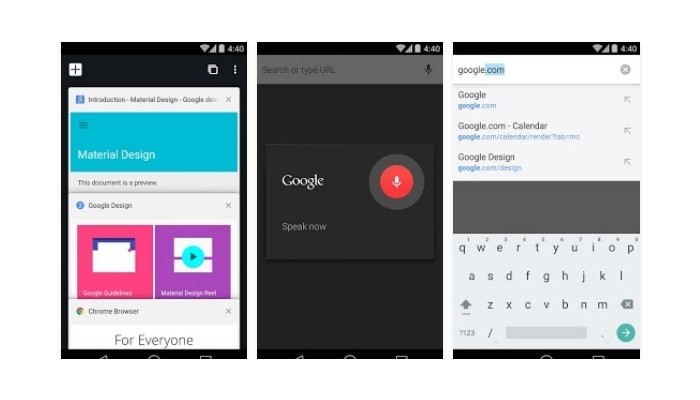
 149Vulnerabilities
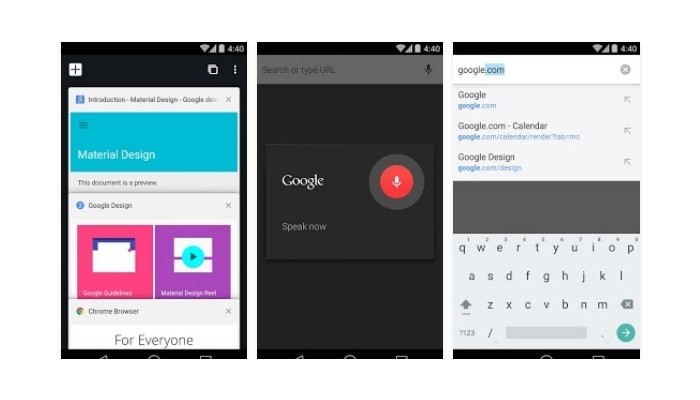
149VulnerabilitiesChrome for Android Has a Hidden Vulnerability, Quite Simple to Exploit
Google’s Chrome staff got in contact with the security researcher and has already started working on a fix A Chinese security researcher...
-
 99Incidents
99IncidentsOz submarine bidders paper over hack attacks, deliver tenders by hand
Report: Germany, France, Japan contract hopefuls spotted multiple attacks. Hacking attempts are forcing bidders in Germany, France, and Japan for Australia’s A$50...
-

 79Data Security
79Data SecurityHIDDEN IN PLAIN SIGHT: BRUTE FORCING SLACK PRIVATE FILES
Last year we switched to using Slack for all our internal communication and it’s working out nicely. It’s very developer centric in...
-

 116Data Security
116Data SecurityTrillions of Facebook posts added to search results
Facebook has indexed almost two trillion posts put on the site by its members to make it easier to find them. The change...
-

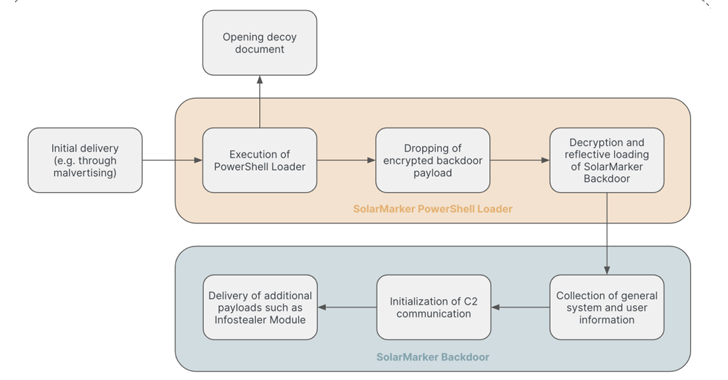
 183Malware
183MalwareMalware Is Using the Dark Web to Stay Hidden
The dark web is well known as a space where anything can be bought or sold: guns, drugs, stolen data, and extreme...
-
 127Malware
127MalwareIntelligent system to check malware hidden in shortened Twitter URLs
Tool to check malware in Twitter URLs to be tested during European Football Championships next summer. An intelligent system has been created...
-

 132Incidents
132IncidentsPorn sites hit by malware hidden in adverts
Security firm Malwarebytes says a campaign of malware hidden inside online ads which hit search engine Yahoo earlier this year has now...
-

 214Geek
214GeekAndroid Ransomware Hidden Behind Fake Pornography App
Android is one of the most vulnerable OS in the world — If you are an Android user you need to be...
-
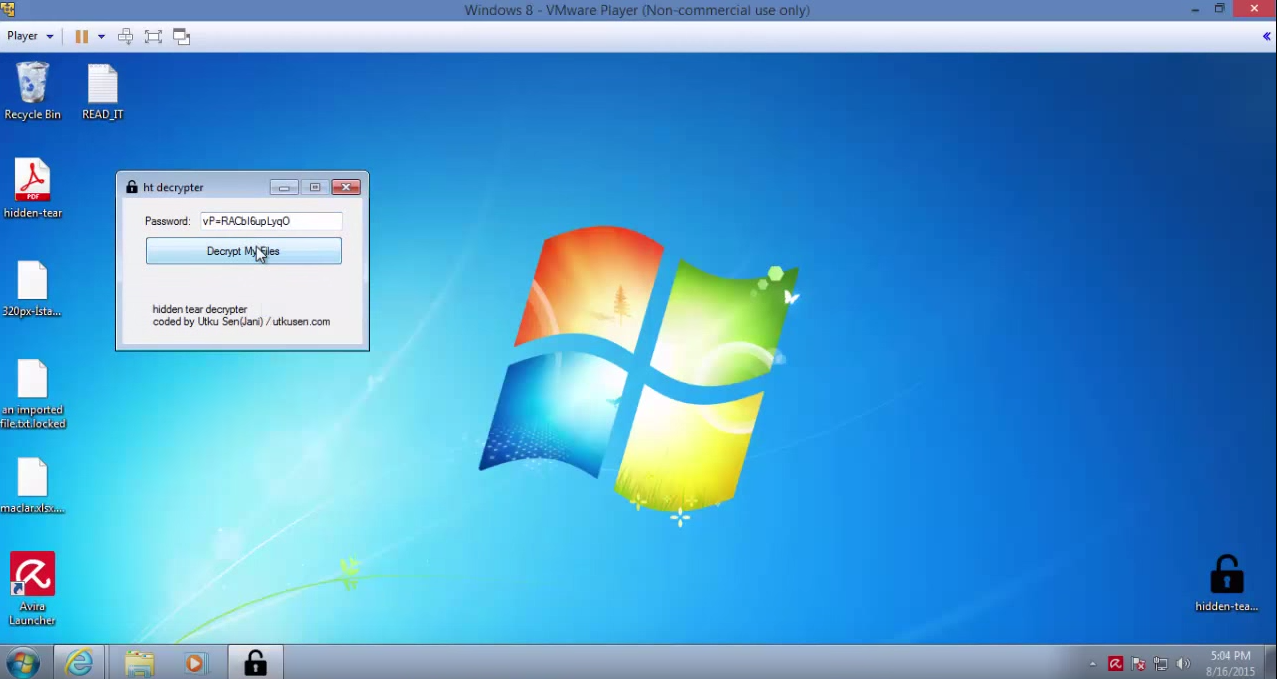
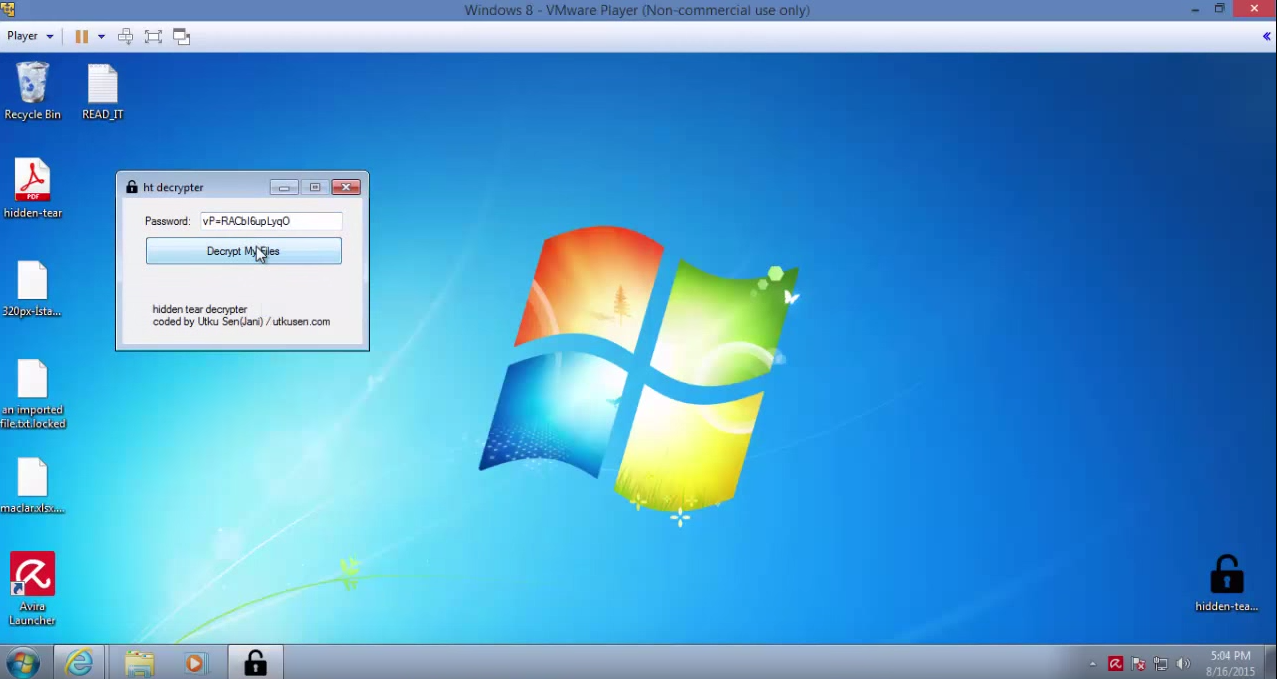 168How To
168How ToHidden Tear – Ransomware-like file crypter
Uses AES algorithm to encrypt files. Sends encryption key to a server. Encrypted files can be decrypted in decryption program with encryption...
-

 108Malware
108MalwareHidden password-stealing malware lurking in your GPU card? Intel Security thinks not
Fears that malware is hiding in people’s graphics chipsets may be overclocked, according to Intel Security. Earlier this year, researchers from the...
-
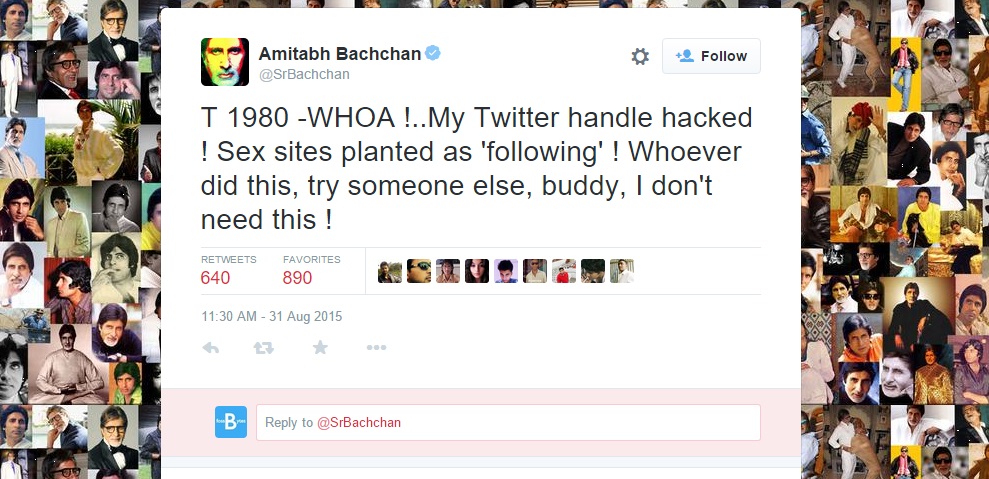
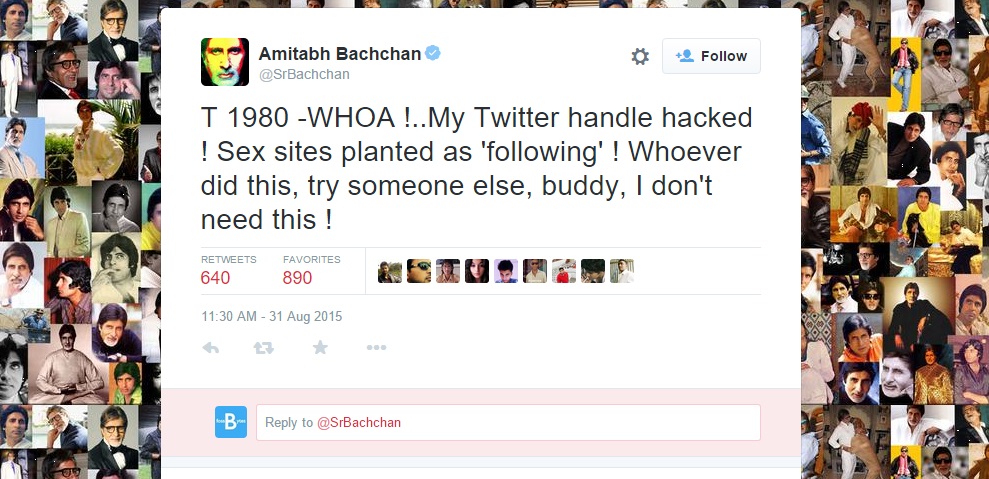 203Hacked
203HackedAmitabh Bachchan’s Twitter Account Hacked, Adult Site Added as ‘Following’
Image: Twitter Short Bytes: The Twitter account of Amitabh Bachchan, Bollywood’s biggest superstar, has been hacked and some adult sites have been...
-

 202Data Security
202Data SecurityHuddersfield teen among six arrested over cyber attack by notorious hacking group
Six teenagers, including an 18-year-old from West Yorkshire, have been arrested on suspicion of launching cyber attacks using a service created by...
-

 170Vulnerabilities
170VulnerabilitiesPatched Ins0mnia Vulnerability Keeps Malicious iOS Apps Hidden
Apple’s monster security update of Aug. 13 included a patch for an iOS vulnerability that could beacon out location data and other...
-

 320Cyber Crime
320Cyber CrimeBeware of New ‘Forbidden Content’ Facebook Phishing Scam Hitting Inbox
Another day, another Facebook phishing scam — Facebook users must be cautious since a new phishing scam message is circulating on the...
-
 398Hacked
398HackedFacebook Friends Mapper: Free Tool Lets You See Facebook Hidden Friends List of Others
In the recent past, Facebook has brought more power to the users and now they can control all the information they’ve shared...
-

 393Data Security
393Data SecurityBanking Malware Delivered via Macro in PDF Embedded Word Document
Delivering banking malware through Microsoft Word documents has been a less common method. However, it is currently being used for spreading malicious...
-

 238Surveillance
238SurveillanceNSA Agents watch Porn in a Special Room to Find Hidden Terrorist Messages
Scrolling through and scrutinizing nightmarish footages of prisoner beheading, children sexual abuse, attacks on American militia, and similar disturbing galleries seems like...
-

 269Data Security
269Data SecurityNew Snowden Documents Expose Canada’s Hidden Cyber Warfare Strength
On Monday, CBC News and The Intercept collaboratively disclosed for the very first time how Canada has endorsed aggressive strategies for attacking,...
-
 348How To
348How ToHow to Enable Hidden Offline Browsing In Google Chrome
Hello everyone, I remember the last time when I shared an article on How To Watch and Download YouTube Videos Offline, someone asked me if I...