Search results for "DDE"
-
 206Hackers Repository
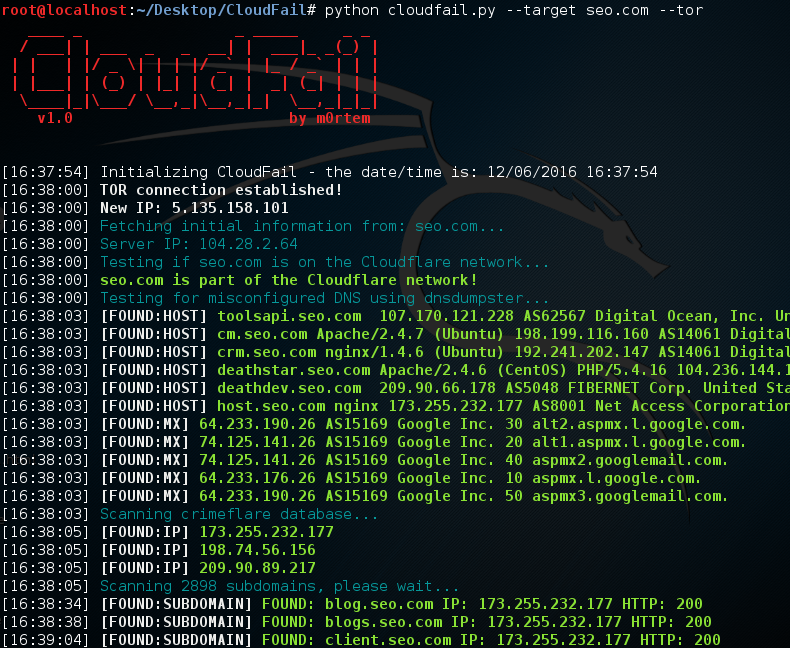
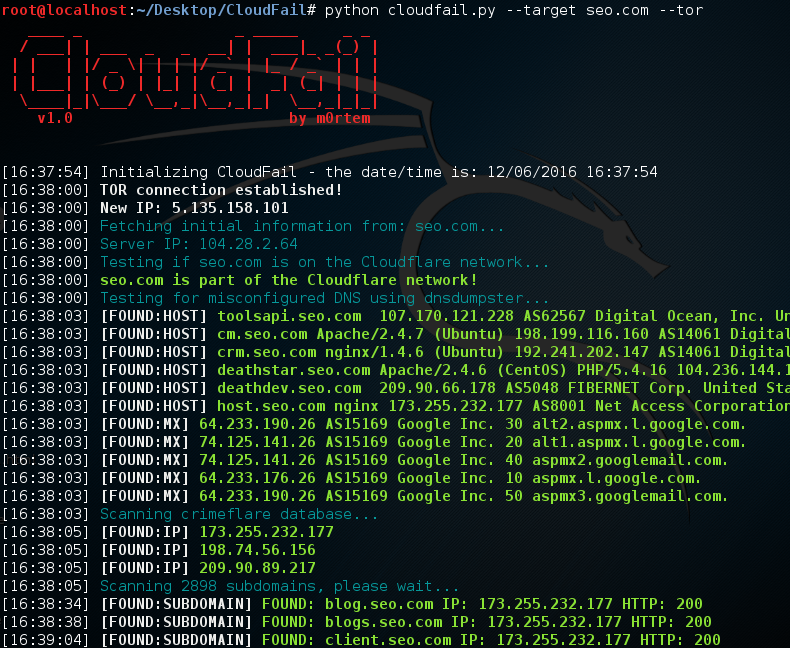
206Hackers RepositoryCloudFail – Utilize misconfigured DNS Find hidden IP’s behind the CloudFlare network
CloudFail Credits: m0rtem CloudFail is a tactical reconnaissance tool which aims to gather enough information about a target protected by CloudFlare in...
-
 260Hackers Repository
260Hackers RepositoryHacking TOR Hidden Services
Hacking TOR Hidden Services What is Tor ? Tor stands for The Onion Route it aims to conceal its users identities and...
-

 119Geek
119Geek10 Android Developer Options Hidden Features For Advanced Users
Short Bytes: At some point, you would have owned an Android device, but have you ever managed to scratch the surface of its...
-

 270Malware
270MalwareBeware: Malicious Payload “Hworm” Dropped Through Embedded Youtube Video’s
A Malware called Hworm Performing multiple Attacks including steal passwords from Firefox, Opera, and Chrome browsers, ability to log keystrokes, kill running...
-

 160Incidents
160IncidentsRansomware hidden inside a Word document that’s hidden inside a PDF
SophosLabs has discovered a new spam campaign where ransomware is downloaded and run by a macro hidden inside a Word document that is...
-

 208Hacked
208HackedCreate TOR’s Hidden .Onion URL Of Any Site With Free EOTK Tool
Short Bytes: Want to create Tor’s hidden .onion URL of a website? A free tool named Enterprise Onion Toolkit (EOTK) can help you...
-

 268Lists
268ListsAndroid Smart Lock: 8 Hidden Ways To Unlock Your Android Smartphone
Short Bytes: Google’s Smart Lock includes various methods to unlock an Android device. You can use voice recognition, facial recognition or a...
-
 103Malware
103MalwareHidden backdoor discovered in Chinese IoT devices
Researchers at Trustwave have uncovered a backdoor in IoT devices from a Chinese manufacturer that could leave them open to exploitation. The...
-

 173How To
173How ToAccess Hidden TV Shows And Movies On Netflix
-

 291How To
291How ToSteghide – Tool To Find Hidden Information And Password In A File
Steghide, is a tool that executes a brute force attack to file with hide information and password established. Linux operating system Steghide Python...
-
 256Data Security
256Data SecuritySteganography Is Very Popular with Exploit Kits All of a Sudden
Steganography, the technique of embedding hidden messages inside public files, has become very popular with exploit kit operators in 2016. Several security...
-
 226Backdoors
226BackdoorsBackdoorMan – Toolkit That Helps You Find Malicious, Hidden And Suspicious PHP Scripts And Shells
A Python open source toolkit that helps you find malicious, hidden and suspicious PHP scripts and shells in a chosen destination, it...
-

 157Data Security
157Data SecurityFBI operated 23 Tor-hidden child porn sites, deployed malware from them
Researcher: FBI was likely enabled to run half of all child porn sites on the servers. As Ars has reported, federal investigators temporarily...
-

 396Lists
396Lists15 Hidden Features in Facebook Messenger You Might Not Know
Short Bytes: Messenger is a popular instant messaging platform. It supports text messaging, voice, and video calls. People can also send photos,...
-
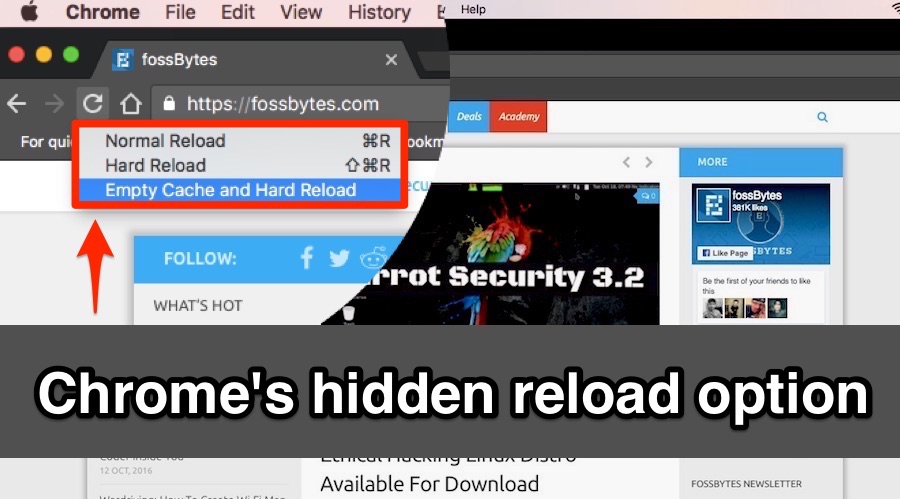
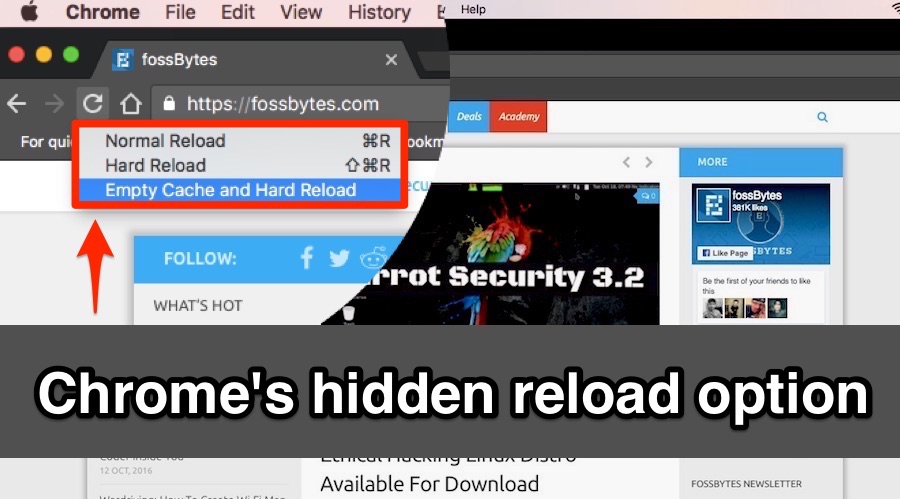 210How To
210How ToChrome’s Hidden Reload Menu: “Normal Reload”, “Hard Reload”, and “Empty Cache”
Short Bytes: Do you know about the “Normal Reload”, “Hard Reload”, and “Empty Cache with Hard Reload” option in your web browser? These...
-
 242How To
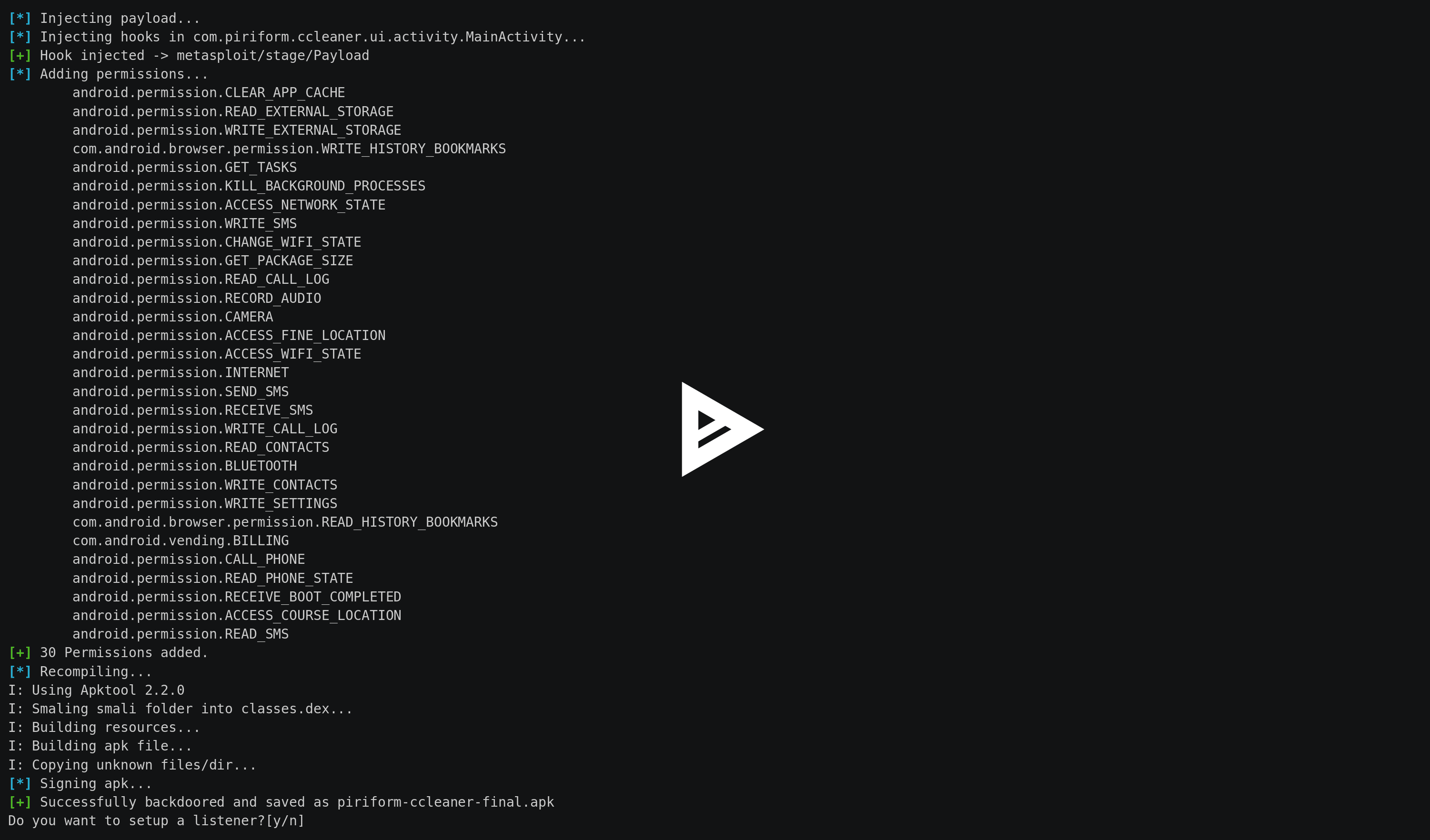
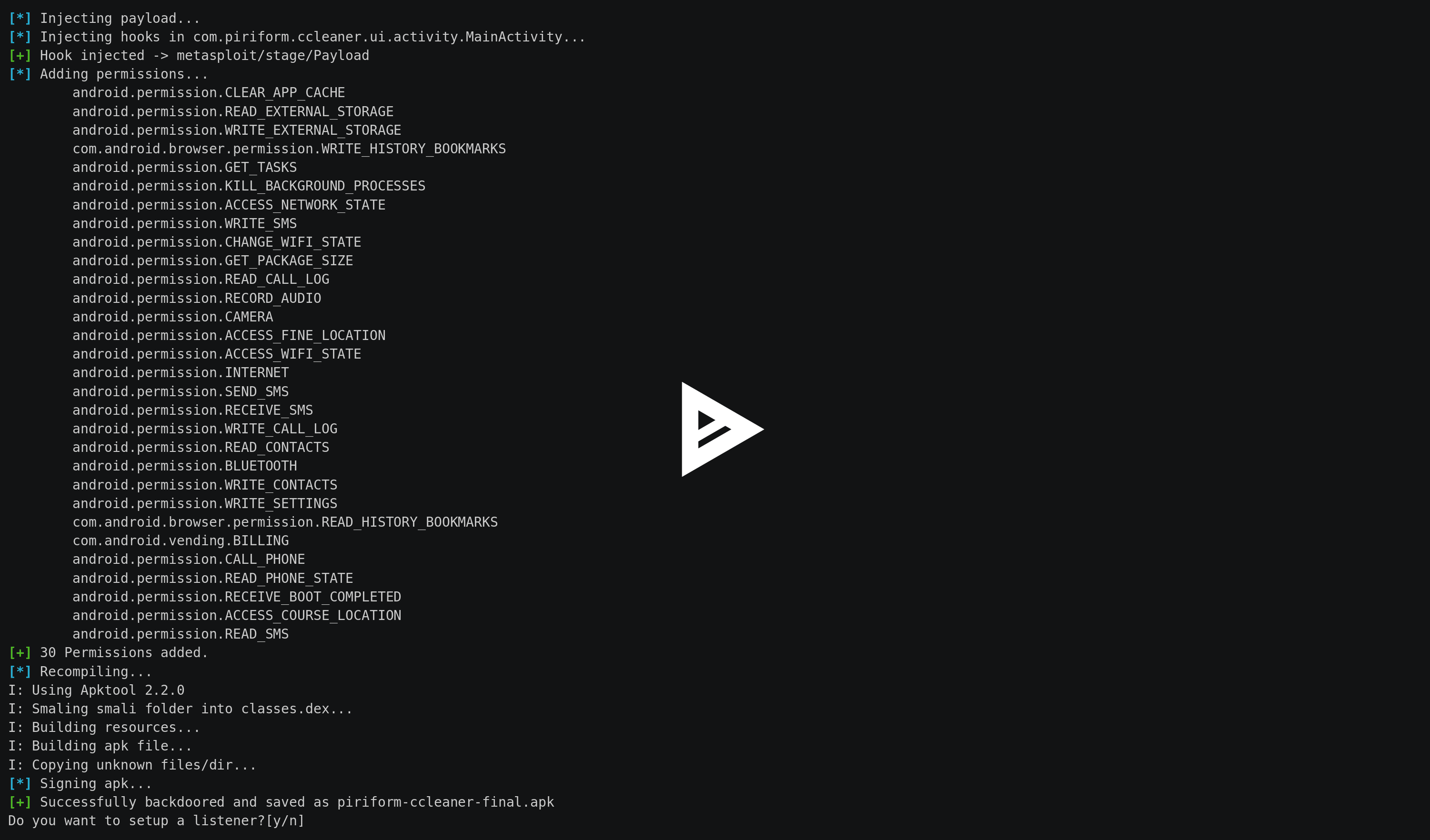
242How ToSpade – Android APK Backdoor Embedder
Quick and handy APK backdoor embedder with metasploit android payloads. Requirements: metasploit Installation and execution: Then you can download smap by cloning...
-
 137Incidents
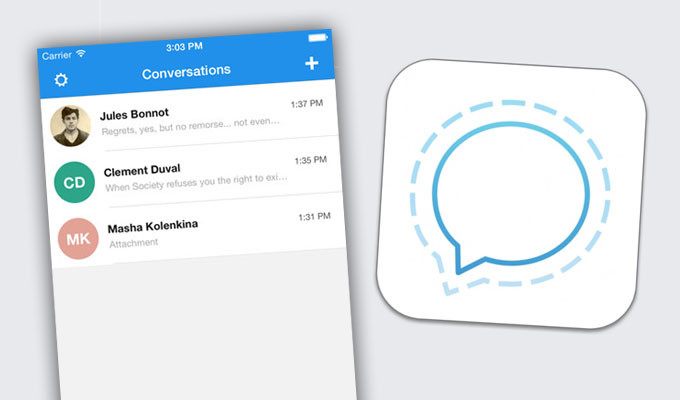
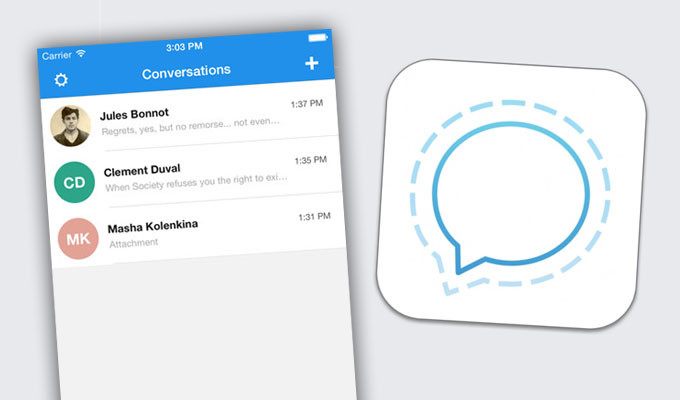
137IncidentsDISAPPEARING MESSAGES ADDED TO SIGNAL APP
The Signal encrypted messaging application on Tuesday added disappearing messages to its array of privacy features. Disappearing messages gives users the ability...
-
 249Geek
249Geek10 Signs That Show There’s A Hidden Coder Inside You
Short Bytes: What are the signs that you should look for before joining a coding class? Apart from the love for programming,...
-
 215Data Security
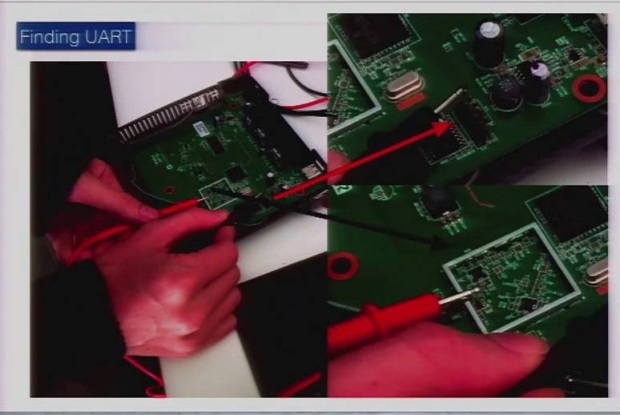
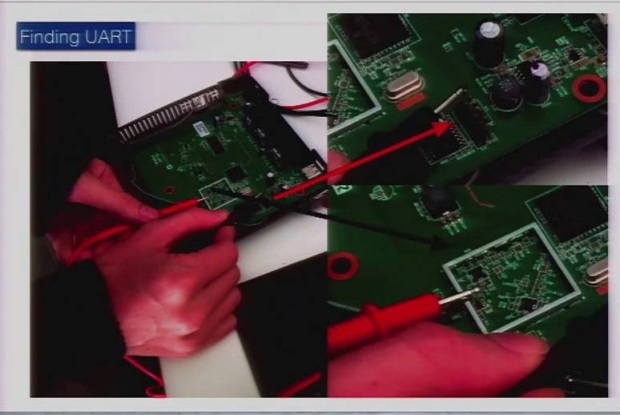
215Data SecurityReversing and Exploiting Embedded Devices (Walking the software and hardware stack)
As technology matures and microprocessors are becoming cheap we are starting to see a trend of products that are now ?smart.? The...
-
 255Incidents
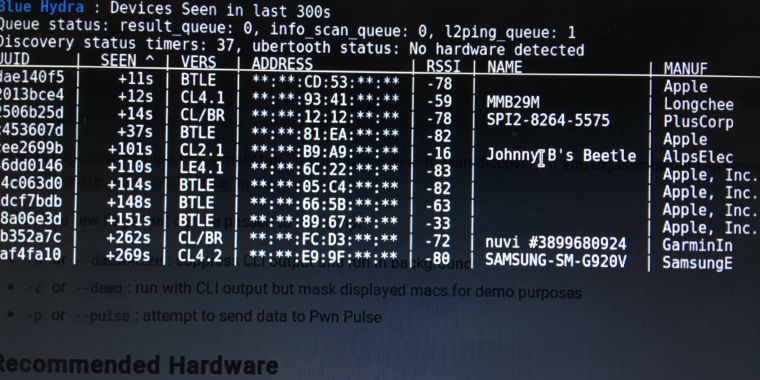
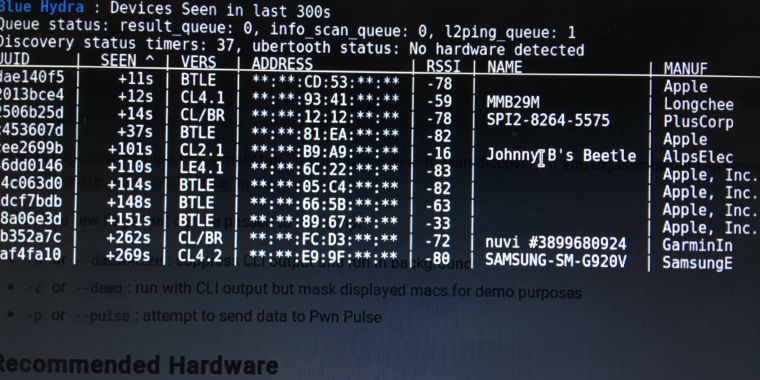
255IncidentsHands-on: Blue Hydra can expose the all-too-unhidden world of Bluetooth
Bluetooth Low Energy devices like smart watches, “wearables,” give you up all day. My new neighbor was using AirDrop to move some files...
-
 207Malware
207MalwareLocky now using Embedded RSA Key instead of contacting Command & Control Servers
According to security researcher Timothy Davies, a new version of the Locky Ransomware, aka Zepto, has been circulating since around the September 5th 2016 that...






