Search results for "DDE"
-
 614Malware
614MalwareFIN7 APT Hackers Added New Hacking Tools in Their Malware Arsenal to Evade AV Detection
Researchers discovered 2 new hacking tools called BOOSTWRITE and RDFSNIFFER that were added in FIN7 groups malware arsenal with sophisticated capabilities and...
-

 526Lists
526Lists11 ‘Hidden’ Android 10 Features We Have Found So Far
The latest Android version has been out for more than a week now, and many of us are working hard to find...
-

 413Infosec
413InfosecShodan and Censys: Finding Hidden Parts On the Internet With Special Search Engines
Our digital lives connect massive things with the Internet. Starting with Smartphones, Wi-Fi routers, Surveillance Camera, Smart TV, SCADA networks and leading...
-

 285Hacked
285HackedThis Innocent USB Charger Is A Hidden Surveillance Camera No One Can See
To tackle uninvited burglars and other intrusions, many people resort to installing closed-circuit TV cameras in their homes. But the problem with...
-

 264News
264NewsApple Could Introduce Face ID On Mac With Added Functionalities
Apple introduced its facial recognition tech dubbed Face ID with the iPhone X, following which all the latest iPhones have it, even...
-

 377Tutorials
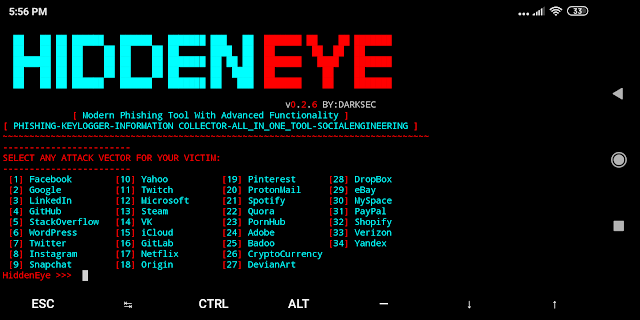
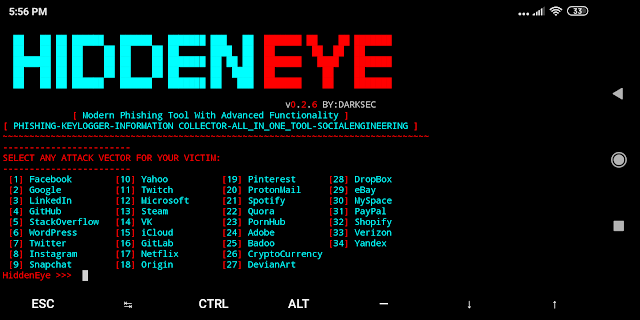
377TutorialsHack your friends Facebook account using HiddenEye
Phishing is what mostly victims fall into trap of fake pages. There are many of methods for creating fake pages. Phishing is...
-
 341Phishing
341PhishingHidden Eye – Modern Phishing Tool With Advanced Functionality
Ultimate Phishing tool with android support available comes with 34 attack vectors of the most popular used services. Hidden Eye Modern Phishing...
-
 276News
276NewsHow To Play The Hidden ‘Tennis Game’ On Google Search?
Wimbledon is coming to an end this weekend. To mark the occasion, Google is offering a new Easter Egg in the form...
-

 337News
337NewsModder Connects External PCIe To Raspberry Pi 4
Raspberry Pi is a low-cost computer designed for tech enthusiasts, students, and engineers who wish to make extreme use of limited hardware....
-

 432Malware
432MalwareMore than 25 million smartphones infected with new malware hidden in WhatsApp
An investigation conducted by system audit specialists from the security firm Check Point has revealed the existence of new smartphone malware; dubbed...
-

 308Incidents
308IncidentsLast Facebook outage exposed users’ images hidden information
Facebook suffered a massive outage in its suite of apps yesterday morning; According to website security audit specialists, this flaw provided social...
-
 203News
203NewsMicrosoft suddenly introduced the Windows 1.0
The Microsoft Windows team released a weird video on Twitter, and the article said that it will launch a new Windows 1.0,...
-

 230News
230NewsExcel Power Query vulnerability puts 120 million users Vulnerable to Remote DDE Attacks
Recently, security researchers at the Mimecast Threat Center discovered a new vulnerability in the Microsoft Excel spreadsheet application, which has caused 120...
-

 543TOR
543TORFreshOnions TorScraper – TOR Hidden Service Crawler
This is a copy of the source for the http://zlal32teyptf4tvi.onion hidden service, which implements a tor hidden service crawler / spider and...
-
 333Malware
333MalwareHackers Use Linux Malware HiddenWasp to Attack Linux Systems for Gaining Remote Access
A new sophisticated, unique Linux malware dubbed HiddenWasp used in targeted attacks against victim’s who are already under attack or gone through...
-
 246Malware
246MalwareHiddenWasp, a dangerous malware that affects Linux systems
Although they are not uncommon, network security specialists mention that the security risks present in Linux systems are not known broadly enough....
-

 229News
229NewsHiddenWasp: New Malware Targets Linux Machines To Control Them Remotely
Unlike the Windows cybersecurity ecosystem, the threats concerning the Linux systems aren’t often discussed in much detail. The attacks either go undetected...
-
 363Malware
363MalwareNew way to detect the malware hidden in hardware
While detecting malicious software hidden in hardware parts is an incredibly complex task, cyber forensics course specialists believe that important steps are...
-

 349Incidents
349IncidentsWall Street Market, drug sales site on dark web, was suddenly closed
Cyber forensics course specialists reported that Wall Street Market, a drugs selling site in dark web, has been closed suddenly, becoming the...
-

 284News
284NewsGoogle to Block Sign-ins from Embedded Browser Frameworks
In a bid to improve its phishing protections and to protect users from MITM attacks, Google has come up with a new...
-
 275News
275NewsGoogle To Ban Embedded Browser Logins To Stop Man-In-The-Middle Attacks
Google will ban logins from embedded browser frameworks, starting June 2019. The reason is the increased risk of phishing hacks using the...






