Search results for "DDE"
-
 2.7KDDOS
2.7KDDOS14 New Vulnerabilities Uncovered In Linux Powered Embedded Devices
On Tuesday 14, the cybersecurity researchers of Claroty and JFrog have detected 14 new vulnerabilities in the BusyBox Linux utility. BusyBox is...
-
 1.2KCyber Crime
1.2KCyber CrimeCouple sold nuclear warship data hidden in peanut butter sandwich
The former Navy Nuclear engineer and his wife used a bubble gum package and peanut butter sandwich to hide SD card with...
-
 3.3KHow To
3.3KHow ToTop 3 Ways to Find a Hidden File on a Mac
Mac computers often have hidden files that you can’t see. Find out the practical ways to find and view the articles with...
-

 2.1KSurveillance
2.1KSurveillanceWhitehat hacker shows how to detect hidden cameras in Airbnb, hotels
The Whitehat hacker and IT security researcher Marcus Hutchins, who saved the world from the WannaCry ransomware attack, has shared simple yet...
-

 3.8KVulnerabilities
3.8KVulnerabilities25 BadAlloc vulnerabilities affects BlackBerry QNX RTOS used by over 195 million vehicles and embedded systems in different industries. Patch quickly
In a security report, BlackBerry announced that its QNX Real Time Operating System (RTOS) is affected by a vulnerability known as BadAlloc....
-

 2.4KMalware
2.4KMalwaremacOS Malware Added New Weapons to Its Arsenal To Attack Google Chrome & Telegram
The security researchers of Trend Micro have recently detected that the XCSSET malware that has been outlined to attack the macOS operating...
-
 4.7KRansomware
4.7KRansomwareREvil Ransomware Gang Suddenly Disappear – Dark Web Sites Are Down
REvil is one of the well-known Ransomware Gangs from Russia which is popular for its earlier and recent ransomware attacks. Apart from...
-

 1.8KMalware
1.8KMalwareInfamous Necro Python bot Added new Tools to Improve Its Chances of Infecting Vulnerable Systems
Nowadays, cyberattacks are increasing rapidly, and as per the report, most cybercriminals are using the automatic bot method to perform all kinds...
-

 695Cyber Attack
695Cyber AttackPakistan-Linked Hackers Added New Windows Malware to Its Arsenal
Cybercriminals with suspected ties to Pakistan continue to rely on social engineering as a crucial component of its operations as part of...
-

 3.6KMalware
3.6KMalwareOusaban: Private photo collection hidden in a CABinet
Another in our occasional series demystifying Latin American banking trojans
-

 2.8KMalware
2.8KMalwareBackdoor added to PHP source code in Git server breach
Had the incident gone unnoticed, the attackers could have taken over websites using the tainted code
-
 5.0KExploitation Tools
5.0KExploitation ToolsByp4Xx – Bypass 403 Forbidden Messages With Well-Known Methods
byp4xx.sh __ __ __ / /_ __ ______ / // / _ ___ __ / __ / / / / __...
-

 3.9KTutorials
3.9KTutorialsHOW TO DETECT HIDDEN CAMERAS OR SPY CAM IN A ROOM
Many users ignore it, but by using their laptop camera or any other camera with a WiFi connection, their MAC address will...
-
 2.0KMalware
2.0KMalwareDigging up InvisiMole’s hidden arsenal
ESET researchers reveal the modus operandi of the elusive InvisiMole group, including newly discovered ties with the Gamaredon group
-
 4.0KHack Tools
4.0KHack ToolsSharpHide – Tool To Create Hidden Registry Keys
Just a nice persistence trick to confuse DFIR investigation. Uses NtSetValueKey native API to create a hidden (null terminated) registry key. This...
-

 2.1KHow To
2.1KHow ToHow To View Hidden Files On MacOS Using Simple Steps?
It’s not just you, we all want to know why the Mac system takes up so much of space. I am curious...
-
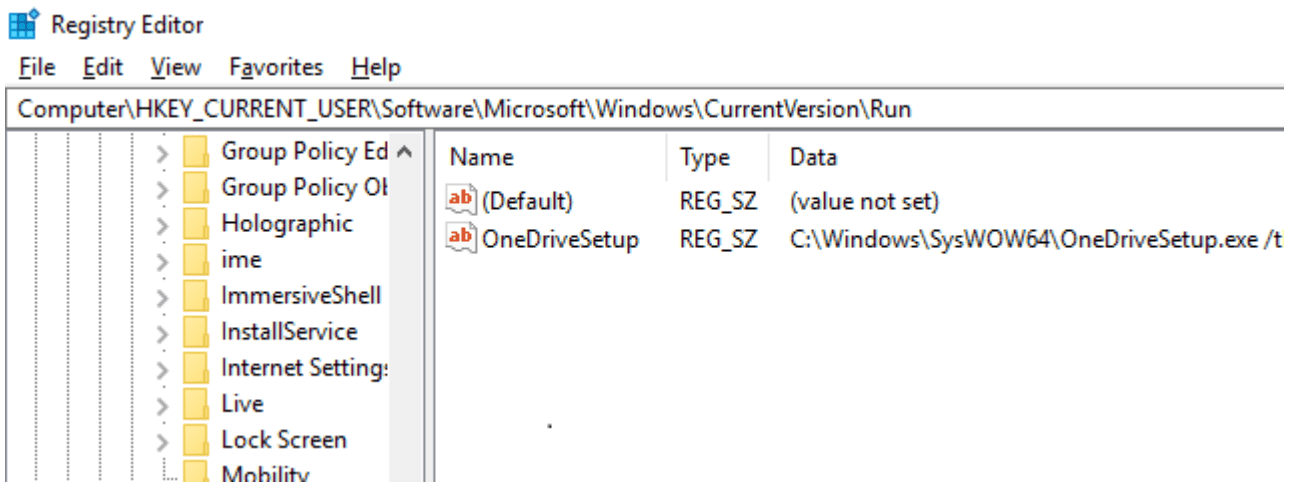
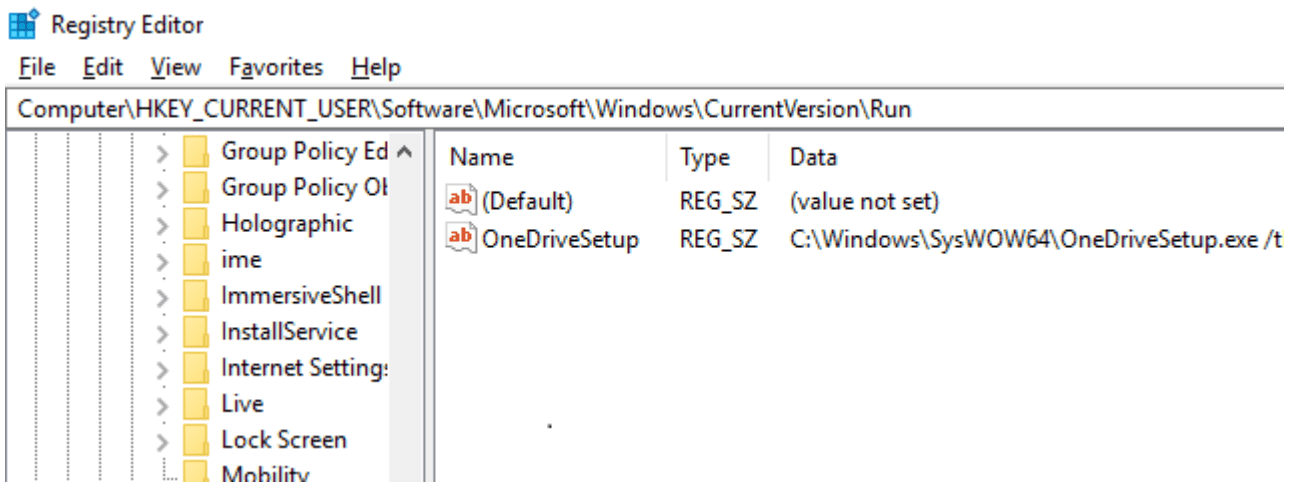 4.9KHack Tools
4.9KHack ToolsSharpHide: Tool to create hidden registry keys
SharpHide Just a nice persistence trick to confuse DFIR investigation. Uses NtSetValueKey native API to create a hidden (null-terminated) registry key. This...
-
 854Malware
854MalwareTitanium APT Hackers Inject New Hidden Backdoor on Windows Using Fileless Technique
A new wave of malware attack strikes again from the Titanium APT group that infects windows with hidden backdoor by mimicking common...
-
Cryptography and Encryption
FOCA – Find Metadata And Hidden Information In The Documents
FOCA (Fingerprinting Organizations with Collected Archives)FOCA is a tool used mainly to find metadata and hidden information in the documents it...
-
 2.1KNews
2.1KNewsBeware! Uninstall These 17 Malware-Ridden iOS Apps Right Now
Malware-ridden apps are common in the Android Play Store, but it seems that Apple is catching up quick. The App Store has...
-
 418Exploitation
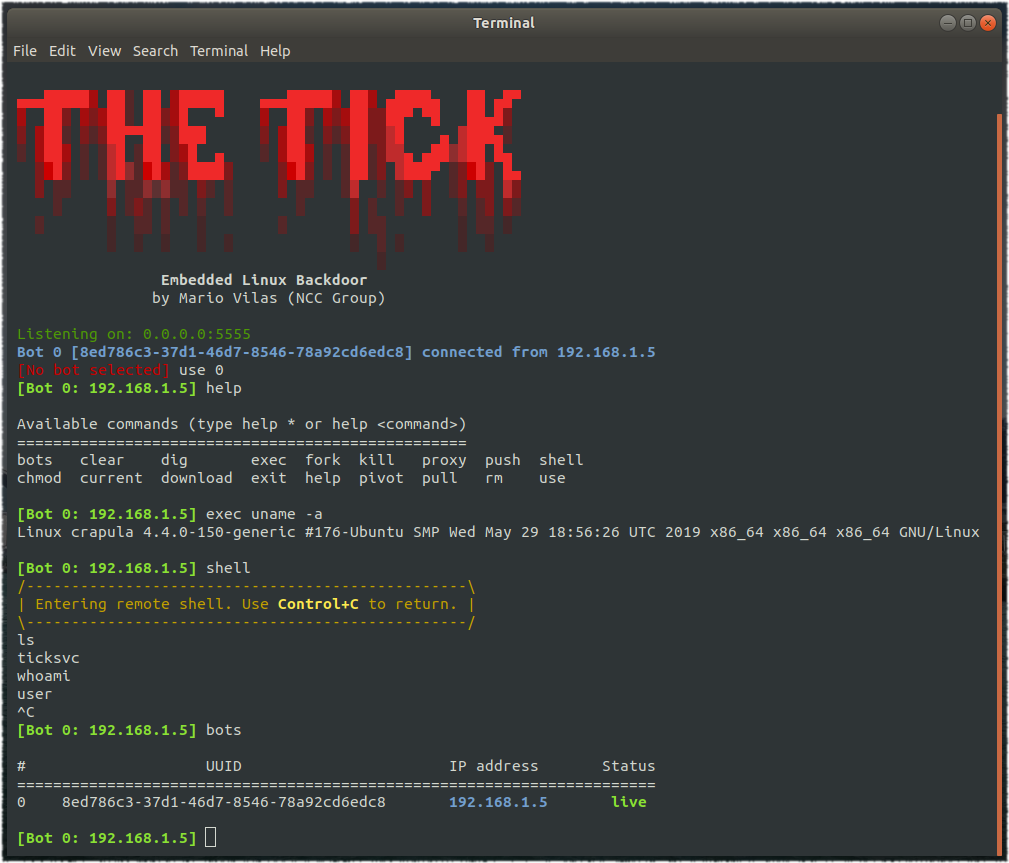
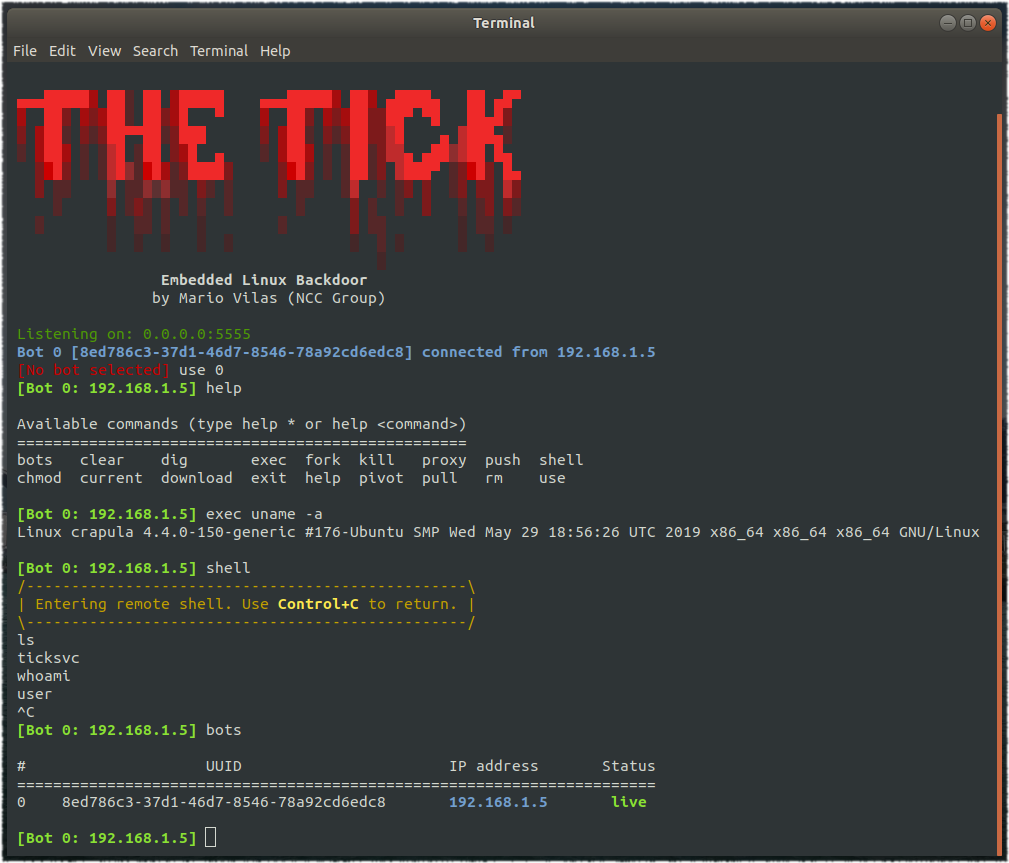
418ExploitationTheTick – A simple embedded Linux backdoor
A simple embedded Linux backdoor. Compiling The Tick depends only on libcurl, so make sure you have the corresponding development package. For...






