Search results for "DDE"
-

 280Incidents
280IncidentsWhat happened after the US moved to chip-embedded payment cards?
Card-Not-Present fraud is still a problem, however. The US began its transition to chip-based credit cards in earnest in October 2015, after...
-
 326Cryptocurrency
326CryptocurrencyHackers Spreading Cryptocurrency Mining scripts via videos that Embedded in MS Office Word Documents
Microsoft word documents abused by Cryptocurrency Mining script embedded phishing Videos and victims tricked into watching an “innocent” video that leads to performing a...
-
Lists
12 Android Oreo Hidden Features You Can Try
Although I have a special place in my heart for this mobile operating system, I won’t say I am aware of every hidden...
-
 468Articles
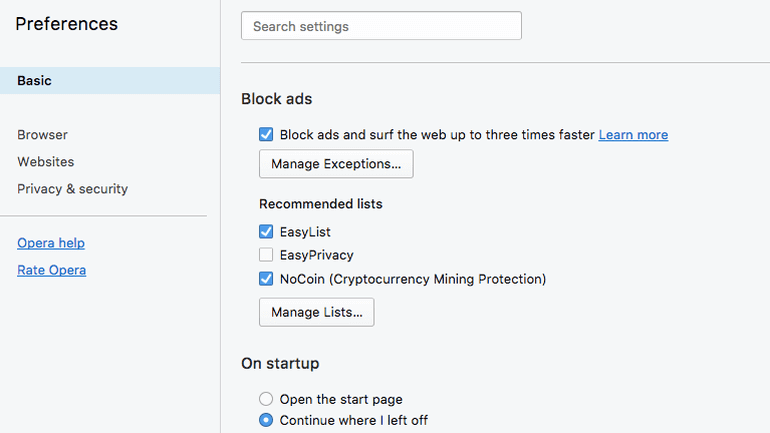
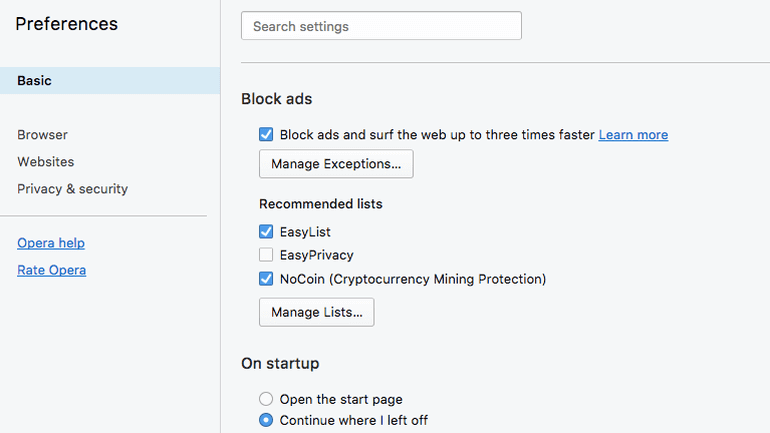
468ArticlesOpera just added a Bitcoin-mining blocker to its browser
Norwegian browser maker Opera has launched the beta version of Opera 50, the first popular browser to integrate a built-in cryptocurrency-mining blocker....
-
 417Lists
417Lists5 Hidden Tips and Tricks for Google Chrome On Android
Google Chrome comes as a default browser installed on most Android phones. It is fast, responsive and comes with all the basic...
-
 217Exploitation Tools
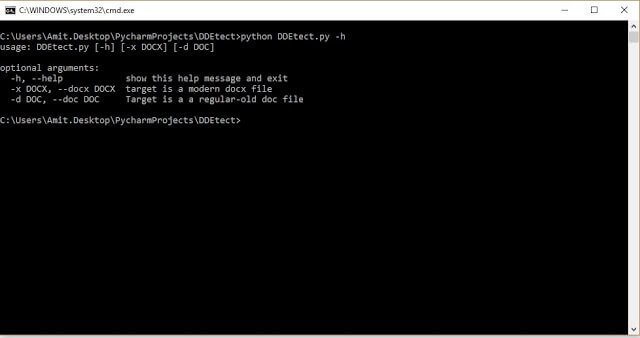
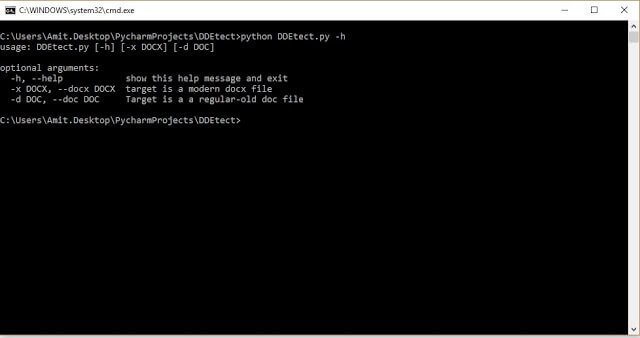
217Exploitation ToolsDDEtect – Simple DDE Object Detector
Written by Amit Serper, @0xAmit DDEtector is a simple DDE object detector written in python Currently supports only word DOCX and legacy...
-

 209Cryptocurrency
209CryptocurrencyHidden Cryptocurrency Miner Coinhive’s Rapid Growth and it’s Prevention Techniques
It is very usual these days to find many applications having a hidden crypto-mining module. But the recent trend is more mainstream...
-
 216Articles
216ArticlesSandboxing support has been added to Firefox for Linux
The Firefox sandboxing innovation confines the browser from the operating system in a way to block web attacks from using a vulnerability...
-
 306Hacked
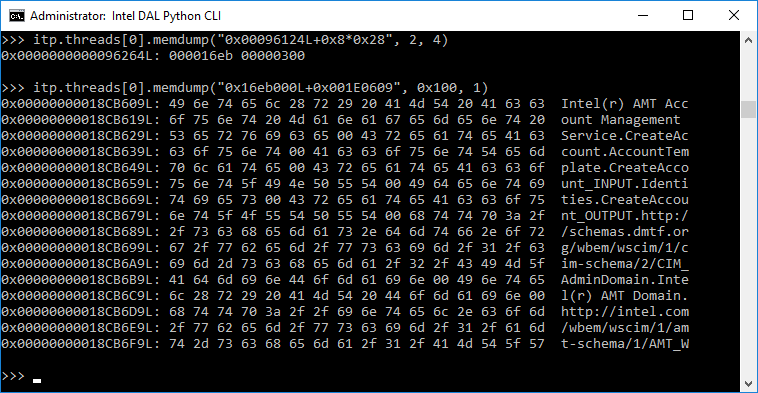
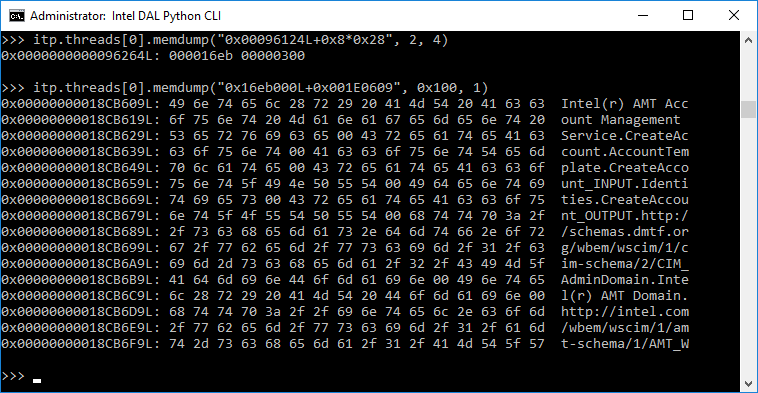
306Hacked“Game Over!” — Intel’s Hidden, MINIX-powered ME Chip Can Be Hacked Over USB
Even the creator of MINIX operating system didn’t know that his for-education operating system is on almost every Intel-powered computer. He is okay...
-

 88News
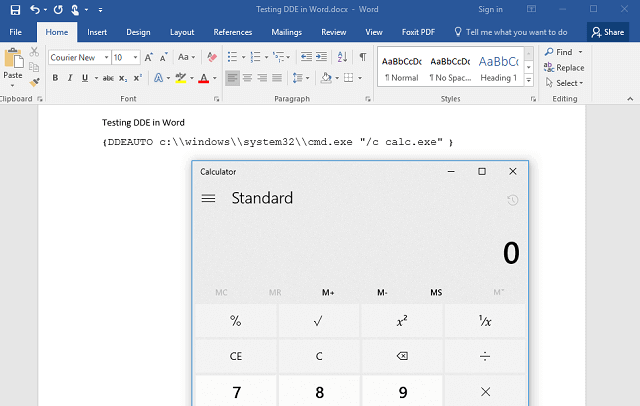
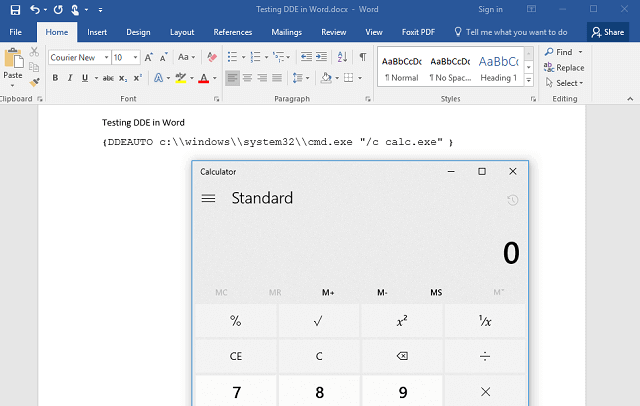
88NewsUnpatched MS Word DDE Exploit Is Being Used In Malware Attacks
A recently discovered MS Word DDE Exploit, uncorrected attack method that exploits an integrated feature of Microsoft Office is currently used in several...
-

 346Geek
346GeekGoogle might block embedded cryptocurrency mining with new Chrome feature
Google Aims to Put an End to Secret Cryptojacking by Making In-Browser Permissions Necessary. In-browser cryptocurrency mining has become the latest obsession...
-
 210Vulnerabilities
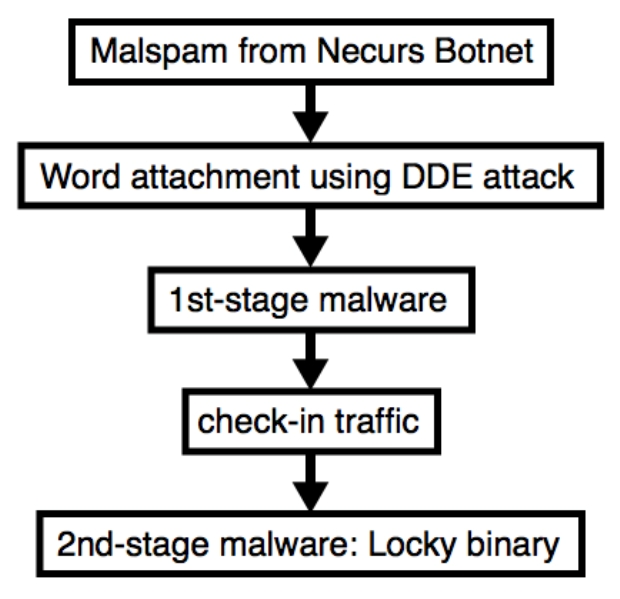
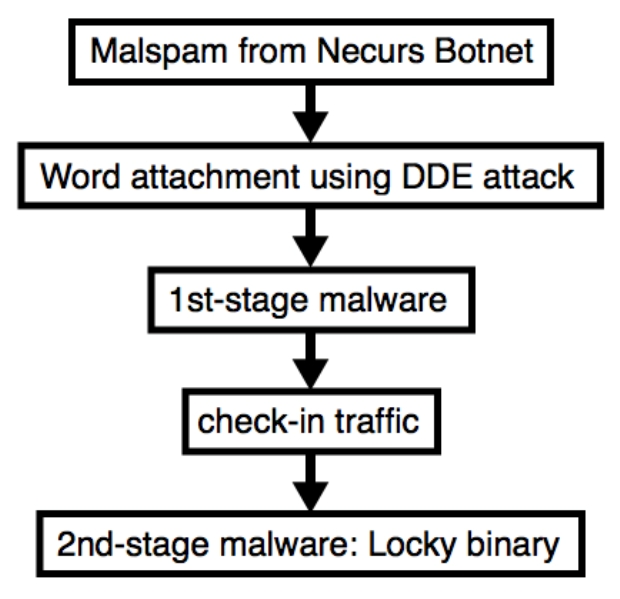
210VulnerabilitiesNecurs Botnet malspam pushes Locky using DDE attack
I’ve seen Twitter traffic today about malspam from the Necurs Botnet pushing Locky ransomware using Word documents as their attachments. These Word...
-
 252Articles
252ArticlesUnpatched Microsoft Word DDE Exploit Being Used In Malware Attacks
A newly discovered unpatched attacking method that exploits a built-in feature of Microsoft Office is currently being used in various widespread malware...
-

 109Incidents
109IncidentsSomeone Created a Tor Hidden Service to Phish my Tor Hidden Service
SMS Privacy is available as a Tor hidden service, and it turns out ~10% of users actually use it that way. This post...
-

 288How To
288How ToHow To Enable Hidden iOS 11 “Dark Mode” On iPhone And iPad?
On September 17, 2017, iOS 11 mobile operating system was released by Apple. The biggest features of iOS 11 included ARKit, improved camera,...
-
 336Geek
336GeekHidden Kill Switch Identified in Controversial Intel ME controller chip
Europe’s leading cyber-security firm Positive Technologies’ security researchers have a bad news for Intel users. They have detected a secret configuration setting...
-
 161Geek
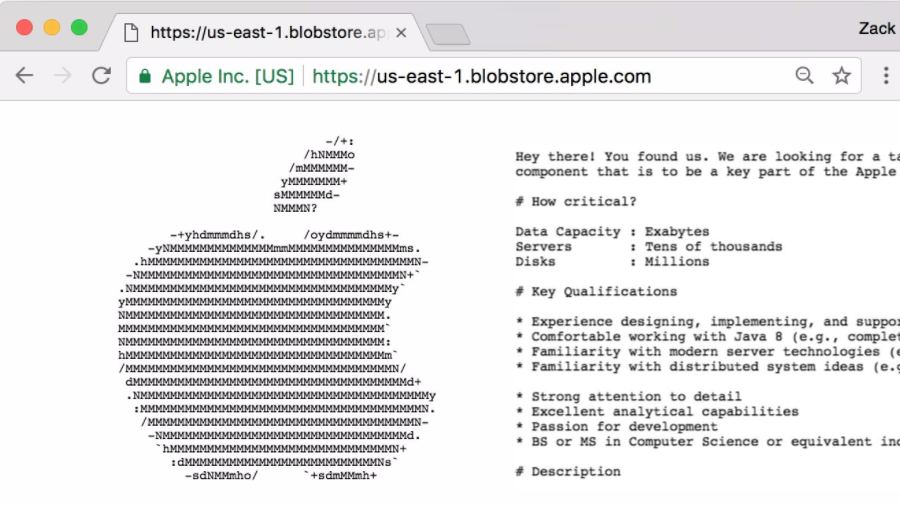
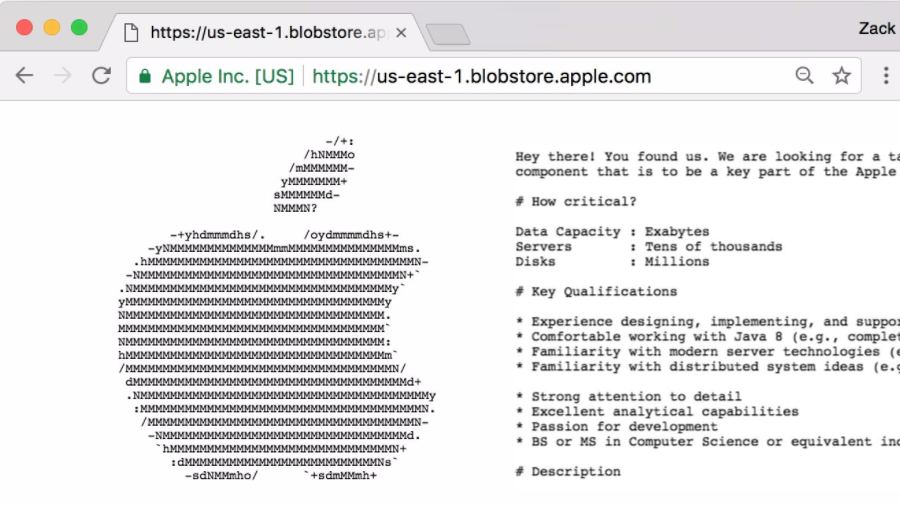
161GeekHey Geeks: Get A Job At Apple By Finding Hidden Postings On Their Website
The biggest tech companies have their rigorous recruitment process to assess the candidates and find if they are suitable for their companies....
-

 330Lists
330Lists11 VLC Tricks & Hidden Features You Must Know
Short Bytes: The name VLC needs no introduction. Although most people perceive it only as a simple media player but hidden beneath...
-

 374Lists
374Lists17 Best Instagram Tricks And Hidden Features You Must Know
Short Bytes: If you love clicking pictures and sharing them with your friends and family, by using some handy Instagram tricks you...
-
 253How To
253How To“Explore Feed”: How To Access Your “Second” And Hidden Facebook News Feed
Short Bytes: Apart from your main News Feed, Facebook offers an option to access a second and hidden feed in its Android...
-

 101How To
101How ToCreating a Hidden Service via Tor for Beginners
Creating a website is pretty simple. Creating a hidden service via Tor isn’t much different. In fact, if you have any semblance...






