Search results for "DDE"
-

 271News
271NewsThis Open Source Extension Displays Hidden Google Search Results
Google receives tonnes of requests from copyright holders daily for removing infringing content. The company then analyzes the received requests and removes the content that violates copyright claims....
-

 324News
324NewsAndroid Q’s Hidden Settings In Pixel Launcher Reveal iPhone-Like Gestures
Google has released the first beta of the upcoming Android Q, and people are frantically searching for new features in the OS....
-

 221News
221NewsMicrosoft Patents Touch Sensor Embedded Fabrics For Surface Devices
According to a patent application, Microsoft’s next-gen Surface devices might include smart fabrics on the back, that would offer standard functionality like...
-
 276Tutorials
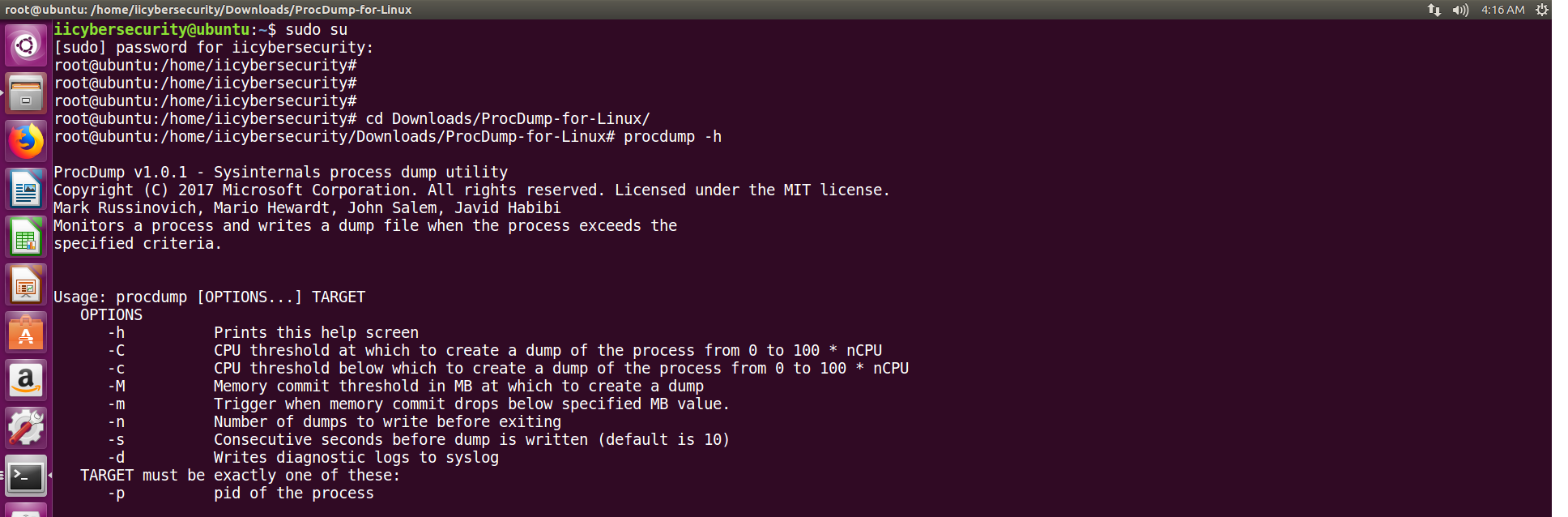
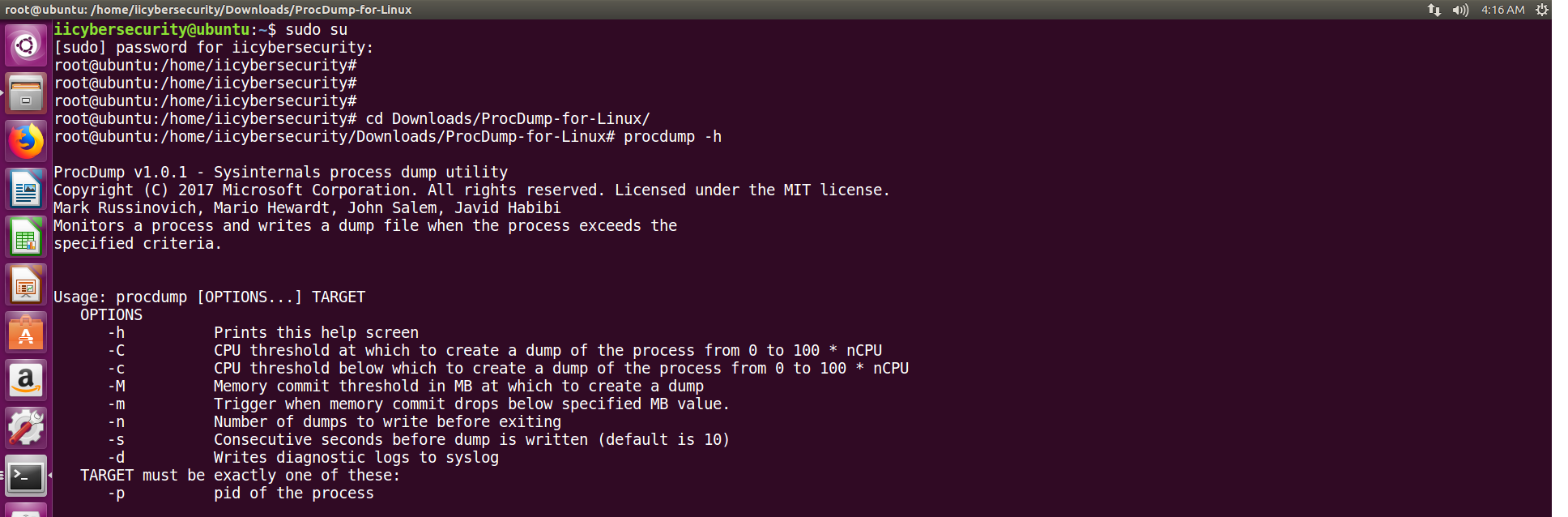
276TutorialsGet hidden details of Any Linux Processes Using Procdump
Core dumps or memory dumps are created when program is executed. A dump consists of modules or work flow that how program...
-

 325News
325NewsTop Free VPN Apps On Android Ridden With Malware And Privacy Leaks
Generally, Android users look out for free VPN apps on Google Play Store as the first step towards protecting privacy. But a...
-

 174News
174NewsNew Android Malware Uses Motion Sensors To Stay Hidden
Security measures are not the only ones seeing improvements! Malicious apps are also figuring out new ways to enhance its working, and one...
-
 359Tutorials
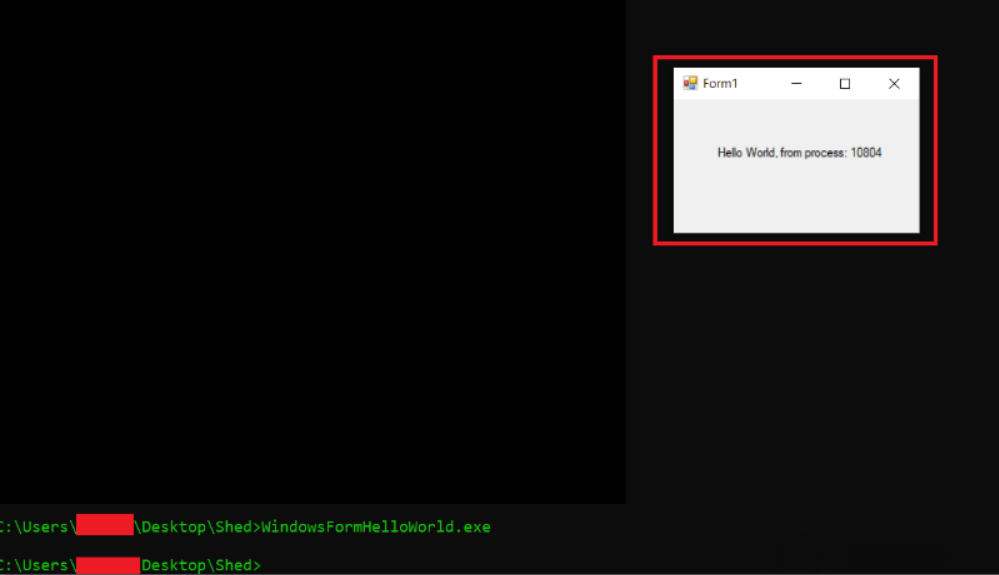
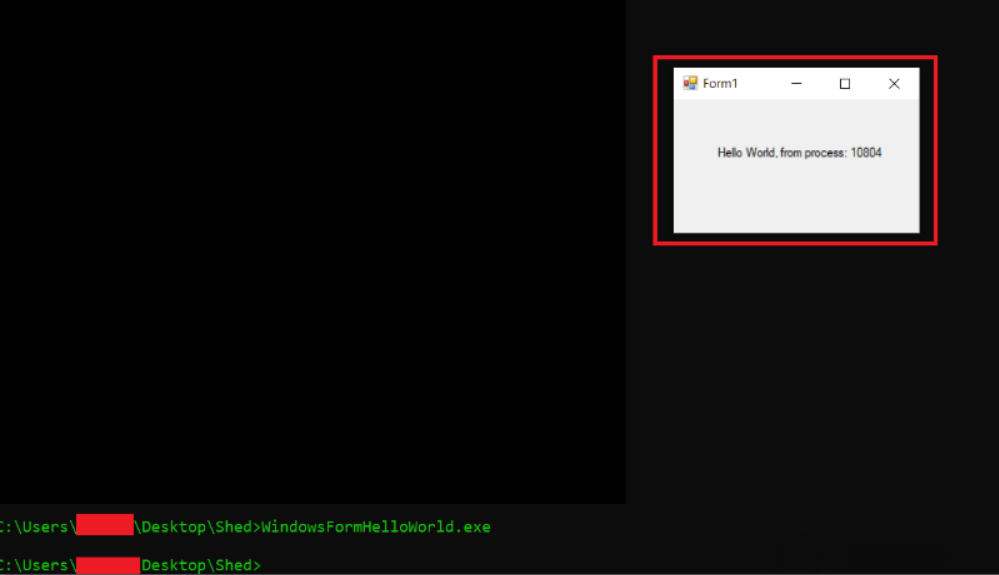
359TutorialsFind hidden malware in .Net program
Information gathering is not an easy task. In many phases, pentester has to go through many tools to gather many information, ethical...
-

 320News
320NewsES File Explorer Has A Hidden Web Server; Data Of 500 Million Users At Risk
When it comes to file explorer apps for Android, ES File Explorer is undoubtedly one of the most popular apps. I, myself,...
-

 343Password
343PasswordStegCracker – Brute-force Utility to Uncover Hidden Data Inside Files
Steganography is an art of hiding messages covert way so that exclusive the sender and recipient know the original message.This technique permits...
-
 314Articles
314ArticlesNew Adobe Flash Zero-Day Exploit Found Hidden Inside MS Office Docs
Cybersecurity researchers have discovered a new zero-day vulnerability in Adobe Flash Player that hackers are actively exploiting in the wild as part...
-
 206Hacked
206HackedThis Hidden Chrome Page Shows All Interstitial Warnings From Google
Hundreds of thousands of dangerous websites are out there on the Internet, waiting for you to trigger malware once you open them....
-
 161Malware
161MalwareCall Recorder App on Google Play with Over 5,000 Installs Contains Hidden Malware Dropper
Malware hidden inside Simple Call Recorder app tricks user in downloading and installing an additional app. Security researcher Lukas Stefanko discovered the...
-

 300Data Security
300Data SecurityFind hidden subdomains with DNSMap
DNSMap: Dnsmap is a tool used to gather subdomains & information of subdomains for a target host, as per ethical hacking courses....
-

 242News
242NewsTimpDoor Android malware turning devices into hidden proxies
Android users in North America are the current target of TimpDoor malware. The McAfee Mobile Research team has identified an active phishing campaign...
-

 194Malware
194MalwareNew Android Malware Turns Your Mobile Devices into Hidden Proxies
Cyber criminals distributing new Android malware via Phishing email campaign that turns infected smartphones into hidden mobile proxies. This malicious app installing...
-
 268Network Tools
268Network ToolsDocker TOR Hidden Service – Easily Setup A Hidden Service Inside The Tor Network
Easily run a hidden service inside the Tor network with this container Generate the skeleton configuration for you hidden service, replace for...
-

 228Malware
228MalwareCryptomining software is hidden as Flash update
A cryptocurrency mining malware is disguised as a Flash update that appears to be legitimate, warn researchers Cryptomining popularity exploded in 2017...
-

 523Malware
523MalwareNorth Korean HIDDEN COBRA Hackers Using New Attack Called “FASTCash” to Cash-out From ATM Machine
North Korean governments sponsored & worlds most famous hacking group HIDDEN COBRA using a new Attack called “FASTCash” to cash out from the...
-
 418Malware
418MalwareNew Adwind RAT Attack Linux, Windows and Mac via DDE Code Injection Technique by Evading Antivirus Software
New Adwind 3.0 RAT (Remote access Trojan) Evolving with new sophisticated capabilities, unlike old version it mainly attacks desktop version of Linux,...
-
 197Malware
197Malware25 Malicious apps that Downloaded More Than 120,000 Times Contains Hidden Cryptomining Script
Malware authors continue to upload malicious apps contains hidden Cryptomining Script to Google play, even though it was entirely banned. Attackers uploaded...
-

 471Lists
471ListsTop 12 Hidden iOS 12 Features Apple Didn’t Talk About At WWDC 2018
With Apple set to release newer models of iPhone, iPad and Apple Watch on September 12 this year, everyone has eyes on...






