Search results for "DDE"
-

 209Ransomware
209RansomwareA New Ransomware Attack Posed as Windows Activator Emerging in Wild With Hidden Functions
A new ransomware distributed by attackers posing as a Windows Activator appearing to be distributed through external network drives. The ransomware found...
-
 294How To
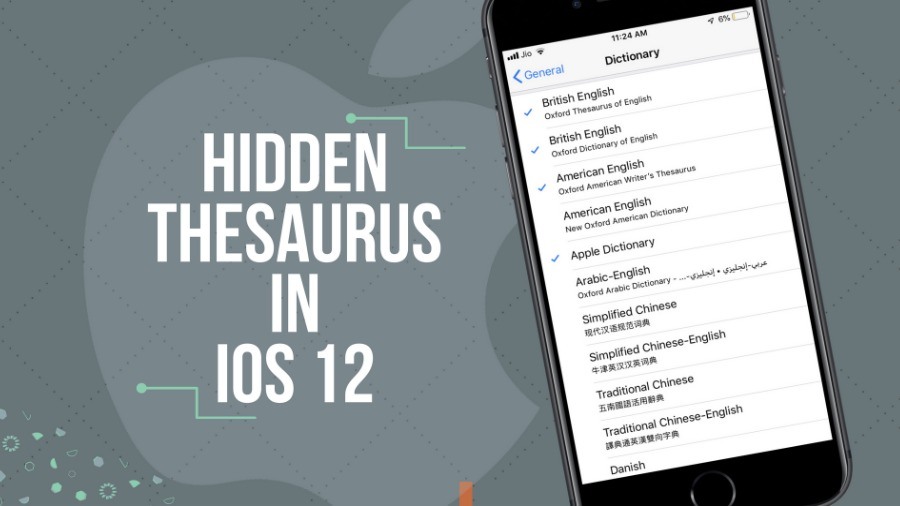
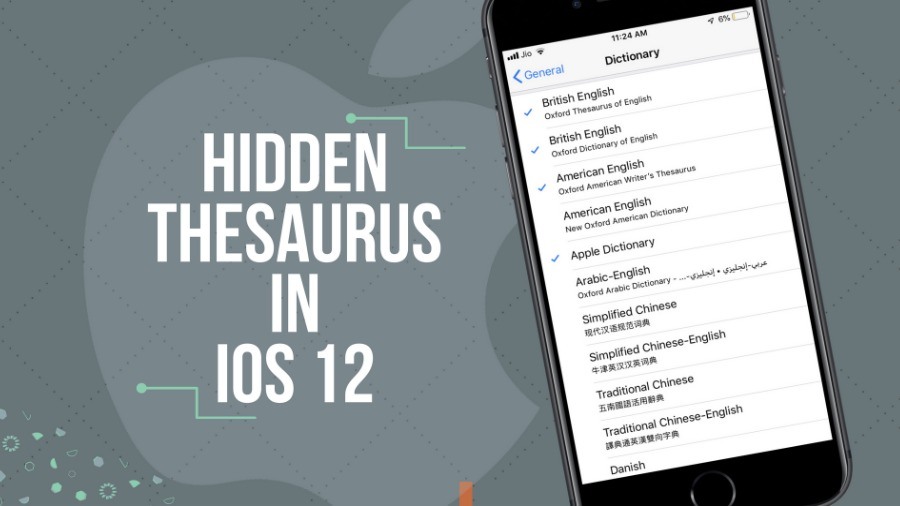
294How ToHow To Unlock And Use Hidden Thesaurus In iOS 12?
iOS 12 is set to roll out next month in Apple’s official iPhone launch event. The latest version of iOS brings many...
-

 361Lists
361Lists9 Android Pie Hidden Features: Best Android 9 Tricks You Might Have Missed
Now that Android Pie is live, there are way too many exciting features to look up to. While some will get easily identified,...
-
 294Bruteforcing
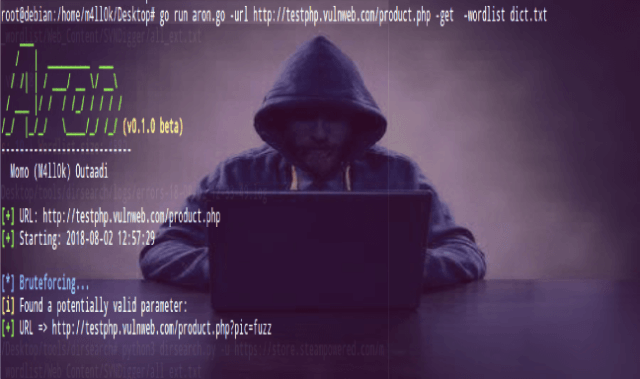
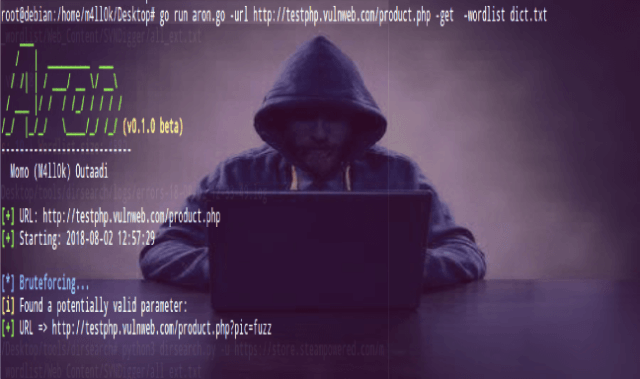
294BruteforcingAron – A GO Script For Finding Hidden GET & POST Parameters
Aron is a simple GO script for finding hidden GET & POST parameters with bruteforce. Aron Installation $ git clone https://github.com/m4ll0k/Aron.git aron...
-
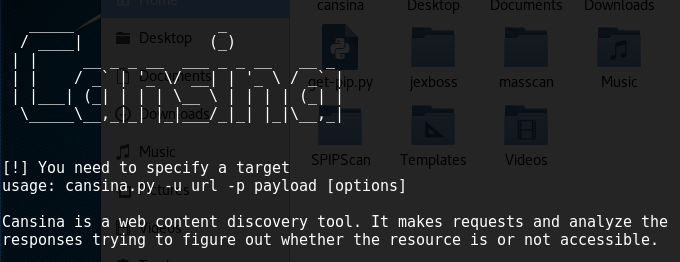
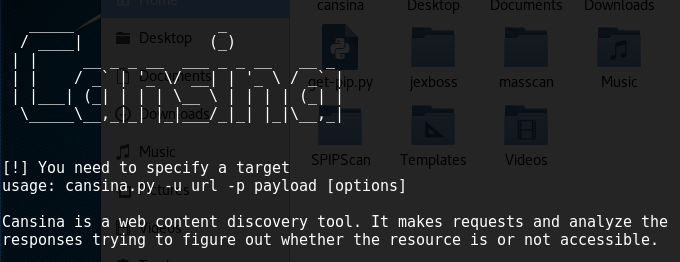 294Hacking Tools
294Hacking ToolsCansina – Open Source Hidden Content Discovery Tool
Reconnaissance is one of the first steps to conduct within a pen test engagement. During this stage, information is gathered using different...
-

 279Hacking Tools
279Hacking ToolsRoutersploit – A Free Framework for Exploiting Embedded Devices
Routersploit is an open source framework used for exploiting vulnerabilities in embedded devices like routers. Routersploit is loaded with various modules that...
-

 166News
166NewsA Hidden Bug In The System Puts 21,000 U.K. Students At Risk
A hidden bug found within an information management system may have compromised the data of 21,000 U.K. schools, who are all now...
-
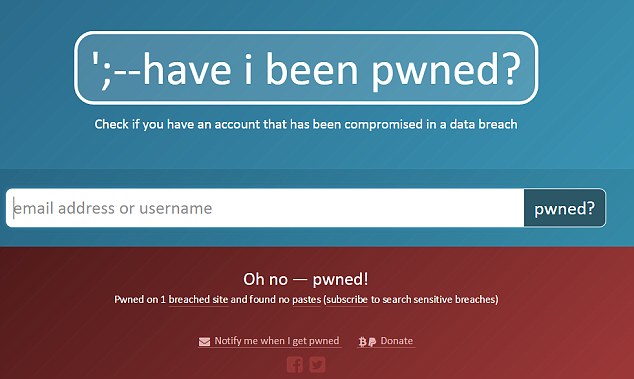
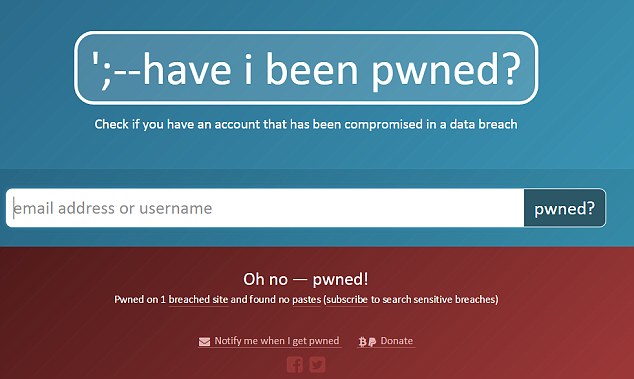 328How To
328How To15.6 million hacked passwords added to “haveibeenpwned” Website version 3
In my opinion, haveibeenpwned is the best website to find out about the security of your password. It has gone through a...
-
 205Vulnerabilities
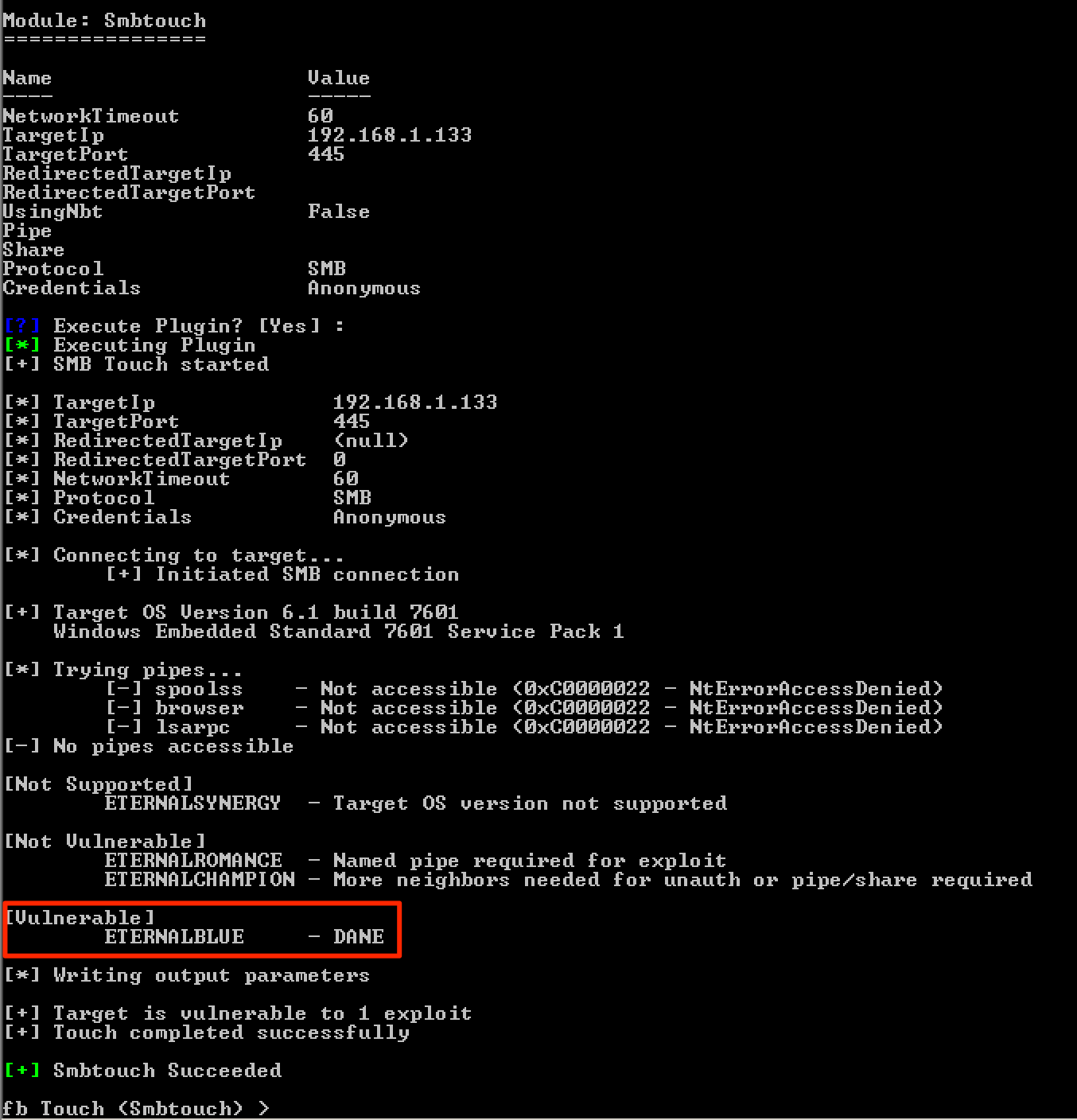
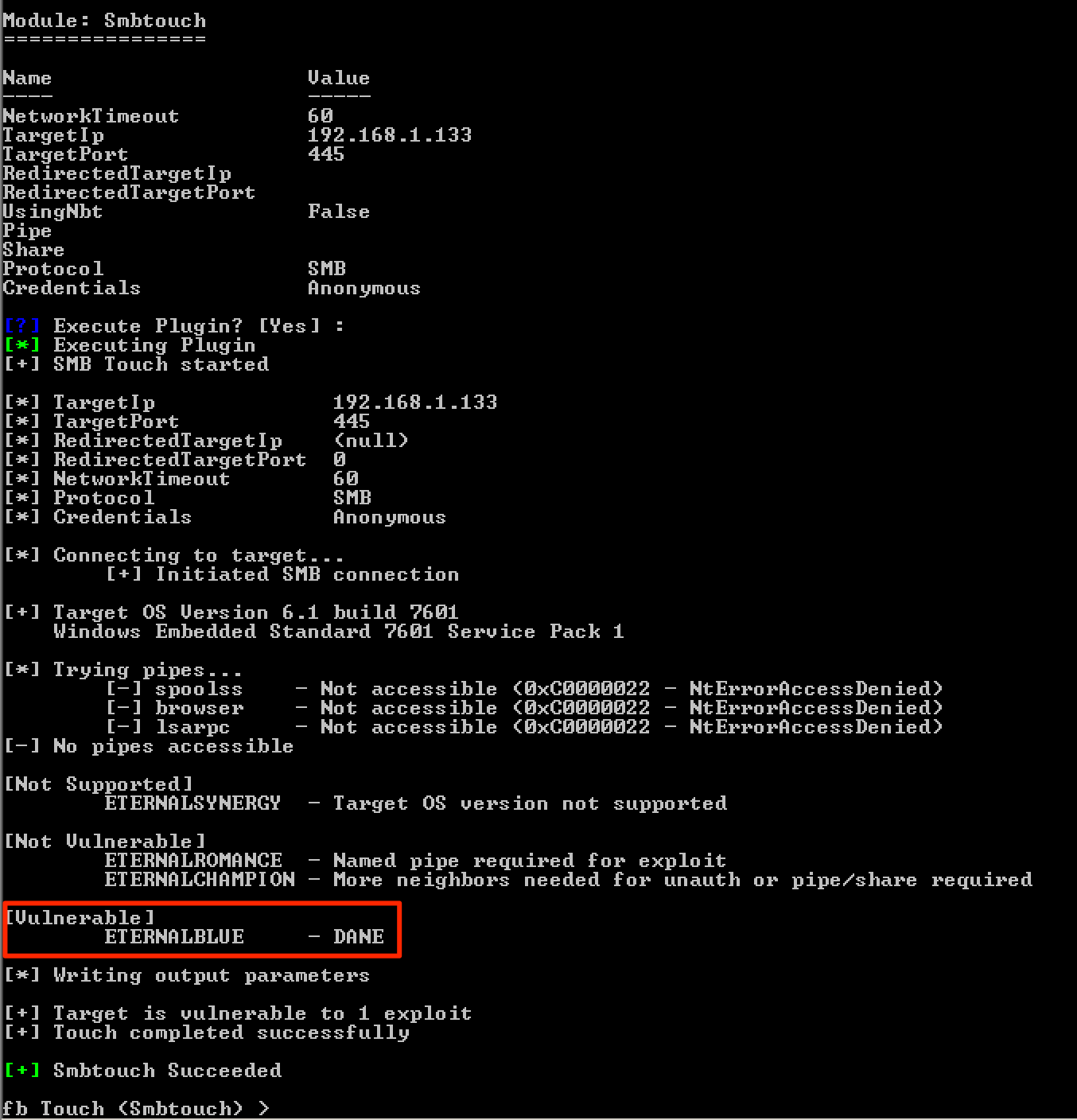
205VulnerabilitiesPatching DoublePulsar to Exploit Windows Embedded Machines
During one of my engagements, I discovered some Windows devices that were affected by the MS17-010vulnerability. One of these devices caught my attention...
-

 355Hacked
355HackedNSA Spying Centers Hidden Inside AT&T Buildings In 8 US Cities
The Intercept, the publication known for its groundbreaking reports, has come up with another revealing piece (via TechCrunch) about the National Security Agency....
-
 390Geek
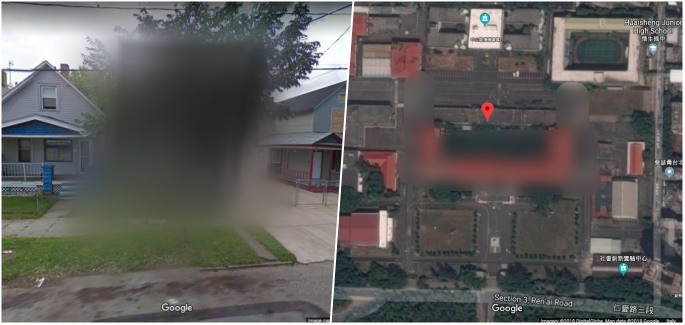
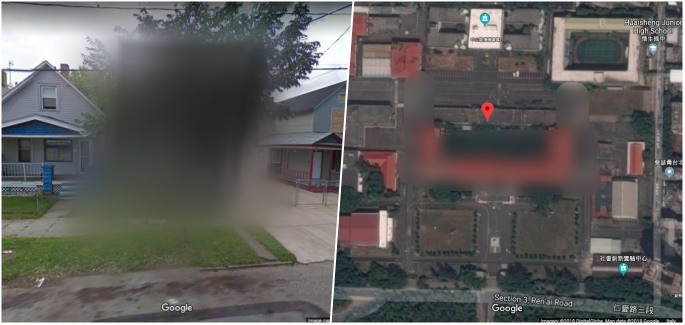
390Geek8 Google Maps hidden places You are not allowed to see
If you thought you have seen it all then you were wrong. In fact, thanks to Google Maps there are plenty of...
-
 224Hacked
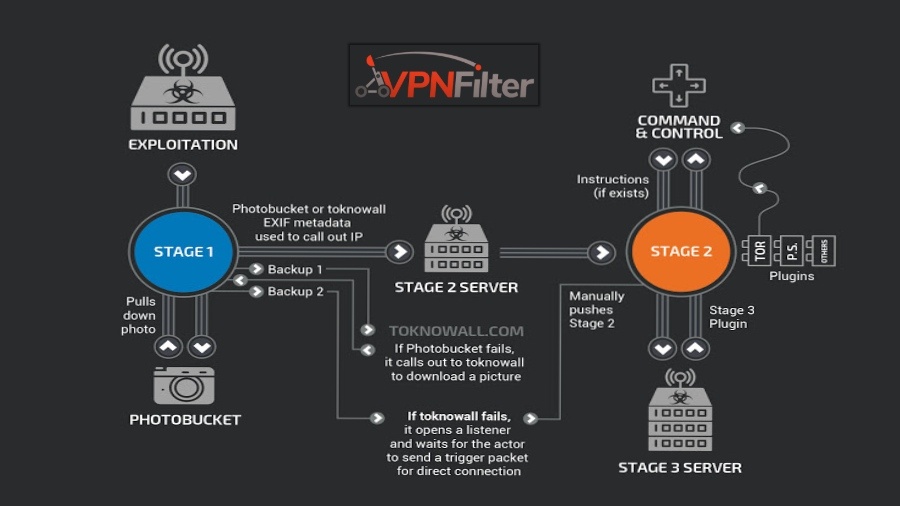
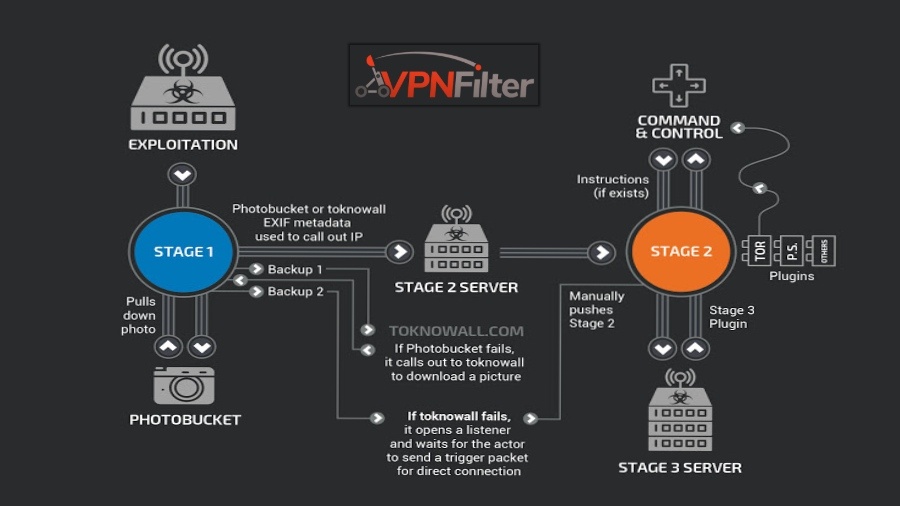
224HackedVPNFilter Router Malware Is Still Alive: More Devices Infected, New Capabilities Added
In late May, Cisco security researchers uncovered a router-hacking malware named VPNFilter, which was reported to infect more than 500,000 consumer Wi-Fi...
-

 609Cyber Attack
609Cyber AttackTwo New Malware Linked To Hidden Cobra Hackers- FBI Issues Alert
The US-CERT issued a joint technical alert from DHS and the FBI, warning that two new identified malware has been used by...
-

 292Malware
292MalwareHIDDEN COBRA – A North Korean Hacking Group Attack in Wide using Powerful RAT & SMB Worm -Warned DHS & FBI
HIDDEN COBRA is one of the well known hacking group who is behind the North Korean government spreading Powerful Joanap Backdoor and Brambul...
-
 229Cryptocurrency
229CryptocurrencyUbuntu Snap Store Apps Contains Hidden Cryptocurrency Miner Malware
An Ubuntu user identified a malicious code that mines Bytecoin (BCN) hidden in the source code of the Ubuntu snap package (2048buntu...
-

 156Malware
156MalwareBackdoor hidden in the npm JavaScript package
According to researchers, the node’s Packet Manager (npm) team just avoided a disaster when it discovered and blocked the distribution of a...
-

 356Cryptocurrency
356CryptocurrencyHiddenminer – Android Monero Mining Malware Can Overheat and Cause Device Failure
A new Monero Mining Android malware dubbed ANDROIDOS_HIDDENMINER that uses the device CPU power to mine Monero malware and could cause the...
-

 336Geek
336GeekHiddenMiner Android Monero Mining Malware Cause Device Failure
Another day, another Android malware – This time, the malware not only comes with Monero mining capabilities but its continuous mining process...
-
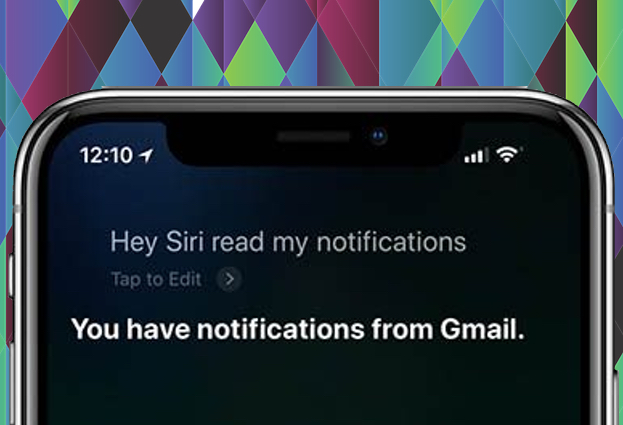
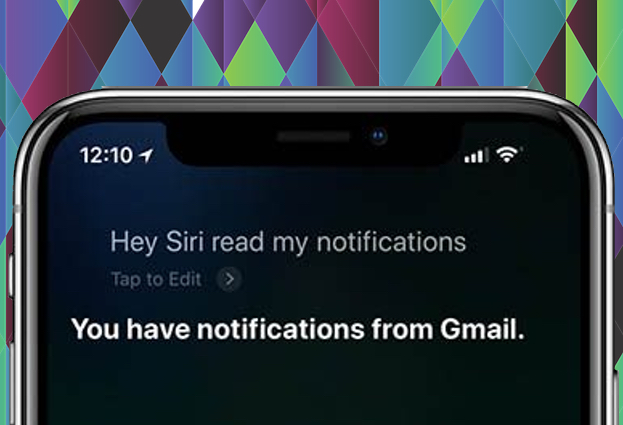 197Privacy
197PrivacyHey Siri! Read me this locked iPhone’s hidden messages…
Messages sent to your iPhone may not be as private as you think.
-

 202Hacked
202HackedHidden For 6 Years, ‘Slingshot’ Malware Hacks Your PC Through Your Router
The researchers at Kaspersky Labs have uncovered a malware, dubbed Slingshot, that has been able to hide for around six years. While...
-

 410Malware
410MalwareWith New Bankshot Malware Cybercrime Group Hidden Cobra Targets Financial Sectors
Hidden Cobra cybercrime group continues to target multiple industries and financial sectors. With this new aggressive campaign, the group implanted Bankshot malware...






