Featured News
-

 202News
202NewsScammers Hack Cricket South Africa Facebook Page with Adult Content
Cricket South Africa page got hacked earlier today where hackers posted racist and sexual content on the page which surprised many of...
-

 254Data Security
254Data SecurityBitcoin’s Creator Satoshi Nakamoto Is Probably This Unknown Australian Genius
EVEN AS HIS face towered 10 feet above the crowd at the Bitcoin Investor’s Conference in Las Vegas, Craig Steven Wright was,...
-

 164Hacked
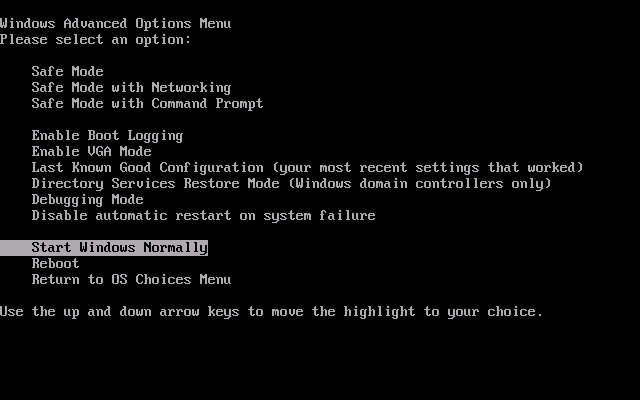
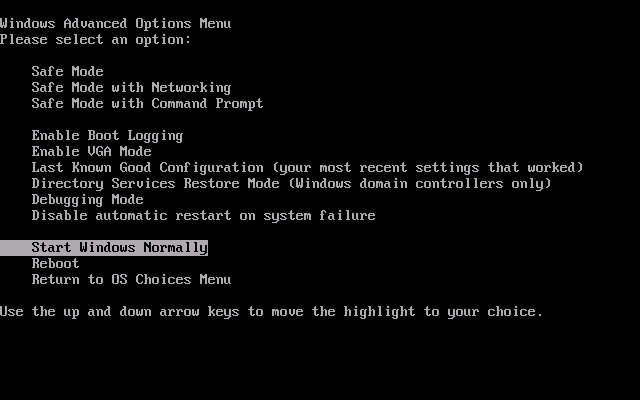
164HackedKudos! Microsoft Does It Once Again
Short Bytes: Microsoft, long known for harbouring different kinds of malware, this time, “unveils” bootkit, a malware which loads even before the Windows...
-
 174Malware
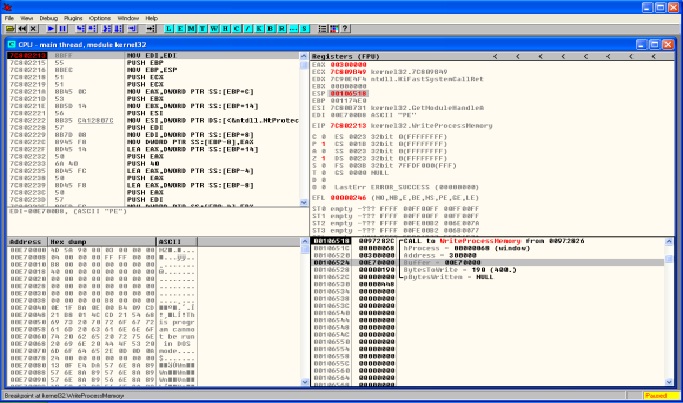
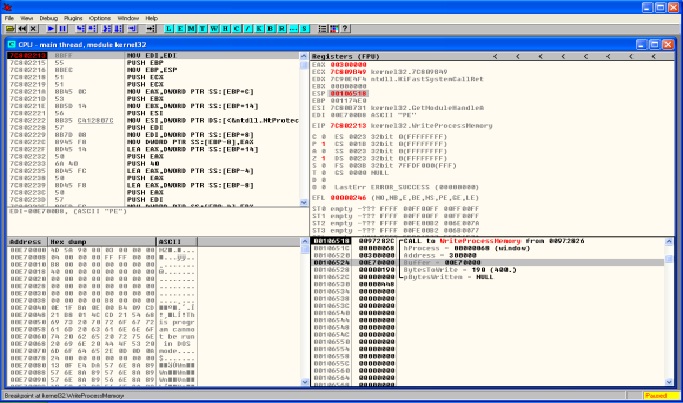
174MalwareMALWARE ANALYSIS – DRIDEX & PROCESS HOLLOWING
Lately the threat actors behind Dridex malware have been very active. Across all the recent Dridex phishing campaigns the technique is the same....
-

 159Vulnerabilities
159VulnerabilitiesApple Patches 50 Vulnerabilities Across iOS, OS X, Safari
Apple has piled on the patches already released by Adobe and Microsoft today, and pushed out updates for iOS, OS X, Apple...
-
 112Incidents
112IncidentsInternet’s root servers take hit in DDoS attack
The internet’s root servers came under a concerted distributed denial of service (DDoS) attack last week that effectively knocked three of the...
-

 271Geek
271GeekNew Facebook Phishing Scam Targets Page Admins
A recent Facebook phishing scam asks users on the social media giant to verify their page because a suspected page forgery was detected...
-

 124Data Security
124Data SecuritySecurity Flaw in Honeywell Gas Detectors Can Virtually Kill People
After hacking nuclear plants, Refrigerator, House Arrest Ankle Bracelet, Smartphones GPS Signals, Electronic Skateboards, Driverless Cars, Jeep, Computer Controlled Sniper Rifle and Jeep Cherokee etc, it is now time...
-

 220Hacked
220HackedContribute Anonymously To Git Repositories Over Tor With Gitnonymous Project
Short Bytes: With gitnonymous project, now you can obfuscate your true identity while making Git commits and pushing to public repositories. Using the...
-
 267News
267NewsPakistani Veteran Journalist Hamid Mir’ Twitter Account Hacked
The official Twitter account of renowned Pakistani journalist Hamid Mir has been hacked by an unknown hacker who is now leaking screenshots...
-

 291Geek
291GeekDisabled Intrusive Win10 Data Collection Features Re-enabled After Nov Update
Windows 10 spying on users is not a new thing nor its force downloading tactics but Windows 10’s November update saw marked improvement...
-

 292Opinion
292OpinionCopyright and social media
ESET's senior research fellow David Harley explores and discusses the main issues surrounding copyright and social media.
-

 135News
135NewsTuneCore Record Label Hacked, Musicians’ Data At Risk
TuneCore, an online music distribution/record label service on Friday, revealed that its database was breached by the hackers and they have been...
-

 210Data Security
210Data SecurityLearn how Eliot from Mr.robot hacked into to his therapist’s new boyfriend’s email and bank accounts
Social engineering is a pretty important item in a hacker’s toolkit.in Mr robot there was a time, we see Elliot, using social...
-

 85Data Security
85Data SecurityPersonal data of Dutch telecom providers extremely poorly protected: how I could access 12+ million records #phonehousegate
On September 11, 2015 I visited Media Markt in Utrecht Hoog Catherijne, a well-known electronics shop in The Netherlands. Since summer 2014, the biggest independent Dutch...
-

 177Opinion
177OpinionWearables: where’s the security risk?
At a recent conference on “the future of wearables” I was asked to speak about security. I think my presentation surprised some...
-

 134Vulnerabilities
134VulnerabilitiesGoogle patches critical vulnerabilities in Android
The flaws can be exploited remotely through emails, Web pages, MMS and rogue apps. Google has released a new batch of security fixes...
-
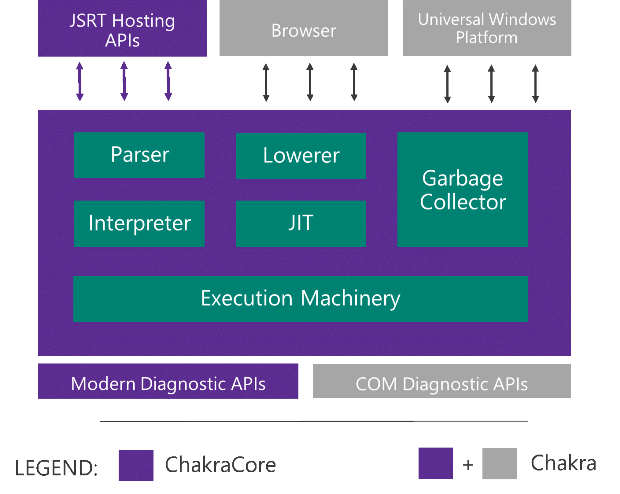
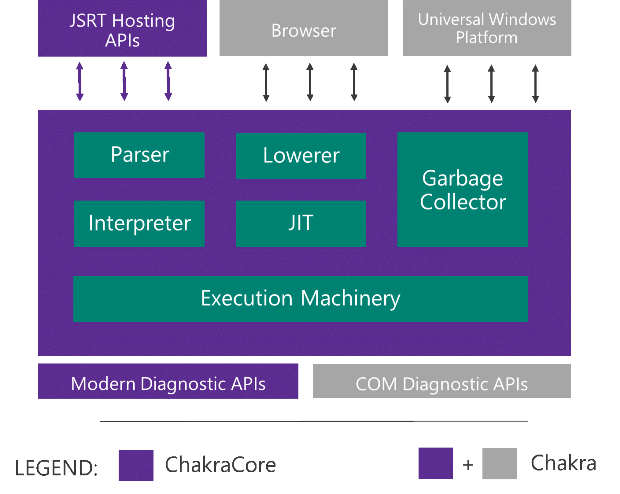 171Data Security
171Data SecurityMicrosoft Edge’s JavaScript engine to go open-source
Today at JSConf US Last Call in Florida, we announced that we will open-source the core components of Chakra as ChakraCore, which...
-

 190Incidents
190IncidentsMalware Steals iOS and BlackBerry Backups via Infected PCs
BackStab technique helps criminals get their hands on your private data, via unprotected phone backups A recent report from Palo Alto Networks...
-
 154Data Security
154Data Security“Nemesis” malware hijacks PC’s boot process to gain stealth, persistence
Bootkit targeting banks and payment card processors hard to detect and remove. Malware targeting banks, payment card processors, and other financial services...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




