Featured News
-

 97Data Security
97Data SecurityMicrosoft’s enterprise security software now offers PUA protection
Microsoft has started to offer potentially unwanted application (PUA) protection in its anti-malware products for enterprise firms. The news means that businesses...
-

 207Vulnerabilities
207VulnerabilitiesCritical Medical Equipment Vulnerable to LDAP and SQL Injection Attacks
Attackers can bypass authentication and access patient data. CERT/CC sounded the alarm on users of the Cardio Server ECG Management System, a broad-scope...
-
 342How To
342How ToFind Problems With Your Wi-Fi Connection Using Ofcom Wi-Fi Checker App
Short Bytes: Facing problems with your broadband connection is a common headache that most people struggle with. The UK telecom regulator Ofcom...
-
 266Hacked
266HackedThis Is The New Shocking Plan Of Anonymous To Mock ISIS Online
Short Bytes: Anonymous is planning to ‘celebrate’ December 11 as an ‘anti-ISIS day of rage’. The hacktivist collective is planning to fill...
-

 96Incidents
96IncidentsAustralia Bureau of Meteorology ‘hacked’
China is being blamed for a major cyber attack on the computers at the Bureau of Meteorology, which has compromised sensitive systems...
-

 197Vulnerabilities
197VulnerabilitiesTech support scams join forces with Nuclear EKs to distribute ransomware
Apparently tech support scams never get old. But they have gotten more aggressive, according to a Symantec blog post penned by researcher Deepak...
-

 93Incidents
93IncidentsGreek banks hit by bitcoin ransom demand
Hackers have targeted three Greek banks for a third time in five days, demanding a ransom from each lender of 20,000 bitcoin...
-

 106Data Security
106Data SecurityPatent Troll Sues Big Companies over HTTPS
ig brands are asked to pay royalties for usage of HTTPS A Texas company filed over 60 lawsuits against big brands that...
-

 260News
260News#Cop21: Anonymous Hacks UN Climate Change’ Webcast Streaming Service Provider
Yesterday HackRead reported how Anonymous breached into the official website of the United Nations Framework Convention on Climate Change (UNFCCC) and leaked...
-

 210Geek
210GeekGroup Fights and Expose Racist Comments on Billboards
A group from Brazil has started an unusual campaign against the people who make racist comments on the Internet. What they do...
-
 220Data Security
220Data SecurityNo backdoor, no service: BlackBerry to exit Pakistan
Blackberry is all set to shut down its operations in Pakistan. The statement came from the company after continuing request from the...
-

 287Cyber Events
287Cyber EventsGoogle Denies Online Censorship Deal with Israel
Google has denied all the accusations that were put forward regarding monitoring or censoring of those YouTube videos that are made for...
-

 111Opinion
111OpinionVirtual machine security – offloading the endpoint
If many endpoints’ traffic pass through the VM host, why not move security there, sort of catch “bad things” before they even...
-
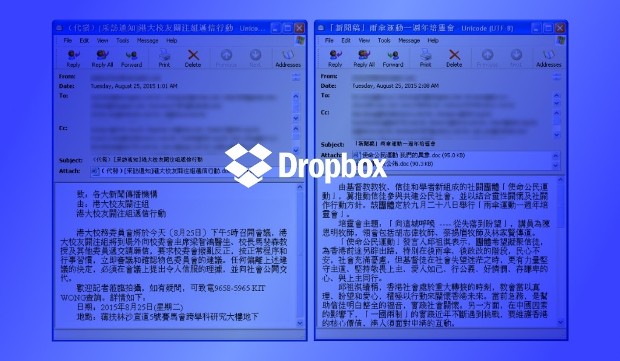
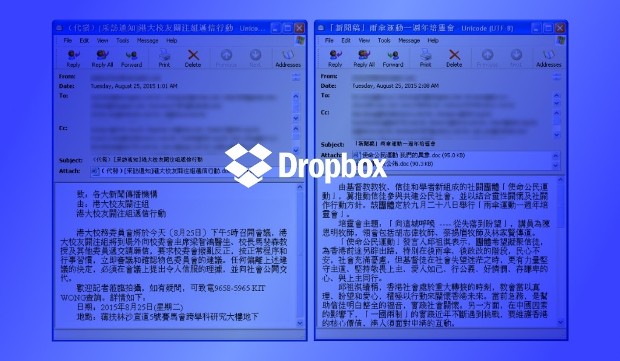 204Malware
204MalwareMalware That Hides C&C Server on Dropbox Detected in the Wild
Dropbox abused by Chinese state-sponsored actors.A malware targeting mass media agencies in Hong Kong was discovered by FireEye’s security researchers. This malware,...
-

 337How To
337How ToHow To Browse Faster On Chrome For Android By Saving 70% Data With New Data Saver Mode
Short Bytes: In the developing markets, making web browsing on mobile a great experience, is a challenging job for smartphone makers and...
-

 104Incidents
104IncidentsHack Brief: Hacker Strikes Kids’ Gadget Maker VTech to Steal 5 Million Accounts
WE’VE BECOME ACCUSTOMED to massive hacks targeting financial and retail institutions, but a recent digital ransacking of a popular kids’ electronics manufacturer...
-

 208Malware
208MalwareCan’t get a break: Pwned Linux ransomware pwned again, infects 3000
Versions one, two, decrypted days after launch. Pwned ransomware Linux Encoder has infected 3000 machines in a month, Russian security firm Dr...
-
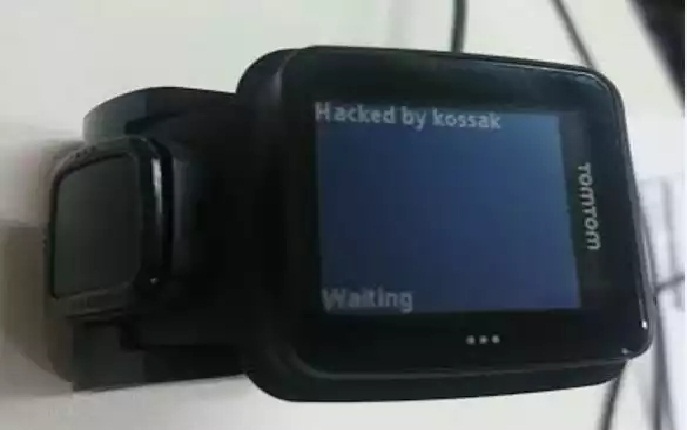
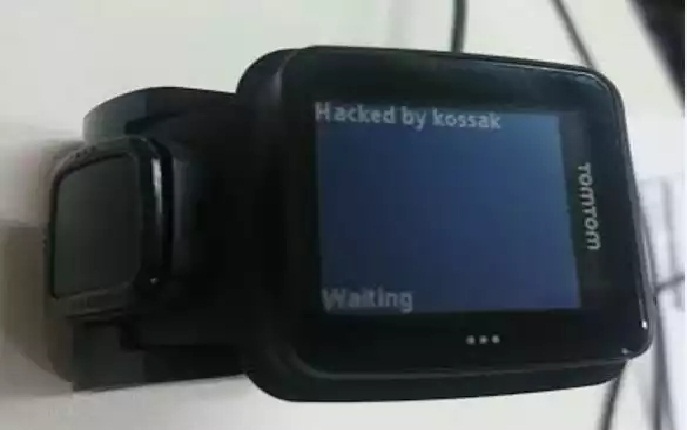 89Data Security
89Data SecurityHacking Smartwatches – the TomTom Runner
I intended originally for this series to contain only three posts, and in order to achieve that, this post is longer than...
-

 236Data Security
236Data SecurityEmbedded Devices Share, Reuse Private SSH Keys, HTTPs Certificates
Researchers have found that thousands of Internet gateways, routers, modems and other embedded devices share cryptographic keys and certificates, exposing millions of...
-

 193News
193NewsAnonymous Hacks UN Climate Change Site Against Police Attack on Cop21 March
The hacktivist group Anonymous breached into the website of United Nations Framework Convention on Climate Change (UNFCCC) and leaked a trove of...
The Latest
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareMalicious Google Ads Pushing Fake IP Scanner Software with Hidden Backdoor
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesGenAI: A New Headache for SaaS Security Teams




