Featured News
-

 325Cyber Crime
325Cyber CrimeRussian hacking group APT28 planned attacks against global banks
A Russian hacking group planned on launching cyberattacks against several banks around the world, according to SC Magazine.
-

 137Mobile Security
137Mobile Security5 signs that an app could be risky
Not all apps are worth your time and money. We Live Security looks at five signs the app you’re about to download...
-

 304Surveillance
304SurveillanceUS House Votes to end NSA’ bulk phone data collection
The USA Freedom Act was passed by the House of Representatives on Wednesday and the bill, which is going to change the...
-
 258Data Security
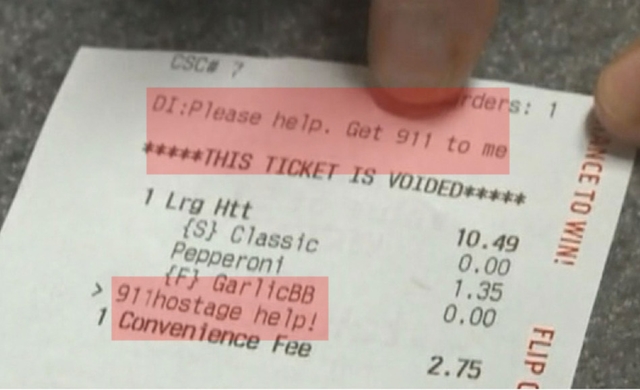
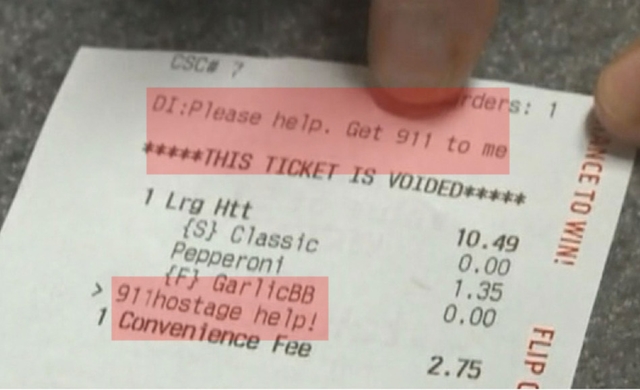
258Data SecurityMother uses Pizza Hut online Order to inform police about hostage situation
A Florida based woman thwarted a dangerous hostage situation by using the delivery instructions section of an online pizza ordering service by...
-

 365Malware
365MalwareJamie Oliver website makes a meal of malware clean‑up
The website of celebrity TV chef and food activist Jamie Oliver has been compromised with malware for the third time this year,...
-

 422Surveillance
422SurveillanceLearn how to download and delete your searches from Google Search
Ever paid attention to how much info Google Search has about you? Well, if you haven’t done so, now you can check...
-

 242News
242NewsPresident of Kenya Website Hacked by Indonesian hackers
On 11th May 2015, the President of Kenya (Uhuru Kenyatta) website was hacked where its homepage was replaced by hackers with one...
-

 97Cyber Crime
97Cyber CrimeThe surprising fees hackers charge for their services
Hackers advertise their nefarious services to potential customers for as little as $90 for Gmail and $350 to access a target's Facebook...
-
 261Cyber Crime
261Cyber CrimeDropbox users hit with ‘urgent, highly confidential’ docs download phishing scam
Dropbox users beware — Cyber criminals are targeting Dropbox users with a fake email, asking them to click on a link to...
-

 245Data Security
245Data SecurityHackers charge $90 to hack Gmail, $200 to $350 for Facebook, WhatsApp
Can you believe there are several online forums who actually claim to provide hackers in case you want to get someone’s Website, Facebook,...
-
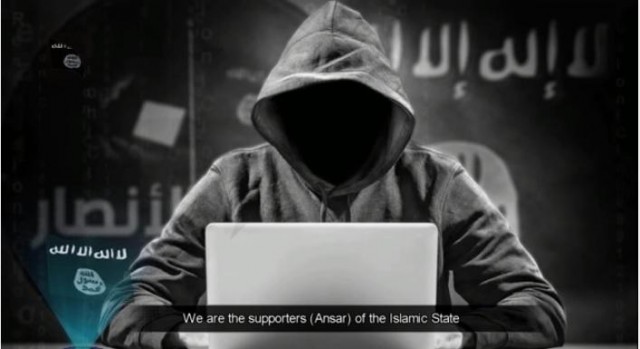
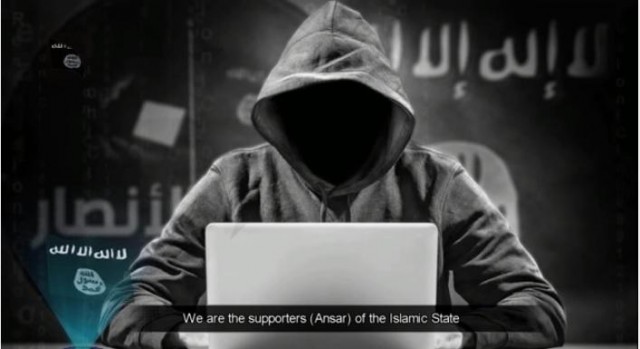 282Cyber Events
282Cyber EventsISIS Hackers Hovering Cyber-attacks, Warning ‘Electronic War’ on US, Europe
In a video released on Monday, Hackers linked with the Islamic State group ISIS are intimidating a chain of cyber-attacks in the...
-

 108Hacked
108HackedEasy-to-use TunnelBear Chrome Extension Brings VPN Services to Everyone
TunnelBear is one of the most loved VPN (Virtual Proxy Network) services because of its simplicity and clean interface. Now, the company...
-

 210Geek
210GeekGoogle suspends Maps editor over peeing Android fiasco
Remember Android logo peeing on Apple logo found on Google Maps in Rawalpindi, Pakistan? Well, Google didn’t like it and for now...
-

 209Data Security
209Data SecurityTeslaCrypt looks like AlphaCrypt Malware uses TOR to transfer ransomware
AlphaCrypt Crypto-Malware the actual mind blower is that it Looks like TeslaCrypt and acts like CryptoWall. the latest piece of ransomware with...
-

 234Hacking Tutorials
234Hacking TutorialsBypass Internet Censorship
Internet censorship is the control or suppression of what can be accessed, published, or viewed on the Internet. It may be carried...
-

 99Malware
99Malware5 practical tips to avoid ransomware in your email
This guide offers you five informative tips on how best to avoid ransomware in your email, which is a common way for...
-

 244Cyber Crime
244Cyber CrimeWhistleblower claims cybersecurity firm extorted clients
A cybersecurity firm is accused of deceiving potential clients in order to extort business, according to whistle blower testimony to the FTC.
-

 208Cyber Crime
208Cyber CrimeFacebook users hit with See ‘What Happens to this Pregnant Lady’ video scam
Facebook’s astonishing “Video Scam” – ‘See What Happens to this Pregnant Lady’ inappropriately misusing “shock element” for users. A post appeared recently...
-

 234Cyber Crime
234Cyber CrimeWhistleblower reveals Cyber Security Firm hacks its own clients to extort them
A former employee of P2P cyber security firm Tiversa, turned whistleblower spilled the beans that the firm hacks its customers in order to fake...
-

 471Privacy
471PrivacyPhotobucket hackers face charges over photo‑stealing app
Two men were arrested last week for allegedly developing hacking software that steals user information and photos from the image-hosting website Photobucket.
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




