Featured News
-
 351Lists
351ListsUse the New Windows 10 Keyboard Shortcuts in Command Prompt
Short Bytes: For Windows Command Prompt users, Windows 10 has brought the gift of keyboard shortcuts. Here, we are going to tell...
-

 311Surveillance
311SurveillancePentagon Plans to Double Drone Flights by 2019 to Expand Surveillance
After momentary calmness, the Pentagon has planned to double the number of U.S. drone flights by 2019. This increment would help military...
-

 103Data Security
103Data SecurityHuge Security Flaw Left Billions of Smartphone Users Vulnerable
A huge security flaw in a Signalling System Number 7 (SS7) left billions of mobile phone users at a risk of eavesdropping....
-

 331Lists
331ListsHere Are The 5 Best Features of Android Marshmallow
Short Bytes: The smartphone maker Samsung has released a nice and colorful infographic telling how your phone will change after Android Marshmallow update....
-

 356Hacked
356HackedWhat Is A DDoS Attack? How DDoS Attack Works?
Short Bytes: DDoS attack is one of the favorite tools used by hackers to disrupt an online service. Here, we are going...
-

 288Lists
288ListsBest Android Torrent Apps to Download Files in No Time
Short Bytes: Today, we are here with the list of the best Android torrent apps to tell you about the most useful...
-

 128Geek
128GeekWoman fined for posting Facebook pic of police car parked at disabled spot
Spain offers a unique gagging law that is now being used in strange ways where people can be fined for posting images...
-

 238News
238NewsHackers Target Saudi Government Websites with “Good Intentions”
A group of hackers going with an online “Cyber of Emotion” hacked Saudi websites with “good intentions.” According to Al-Riyadh newspaper, more than 24...
-

 255Hacked
255HackedYour BitTorrent Client Can Be Exploited for DoS Attacks, Research Warns
Short Bytes: According to a new research, your BitTorrent client and BitTorrent Sync can be targeted and successfully exploited for DoS (Denial...
-

 308Cyber Crime
308Cyber CrimePayPal Customers Hit with ‘Changes to Legal Agreements’ Phishing Scam
A PayPal phishing scam can be tricky, but don’t worry all you need to do is keep your eyes open and do what...
-
 219How To
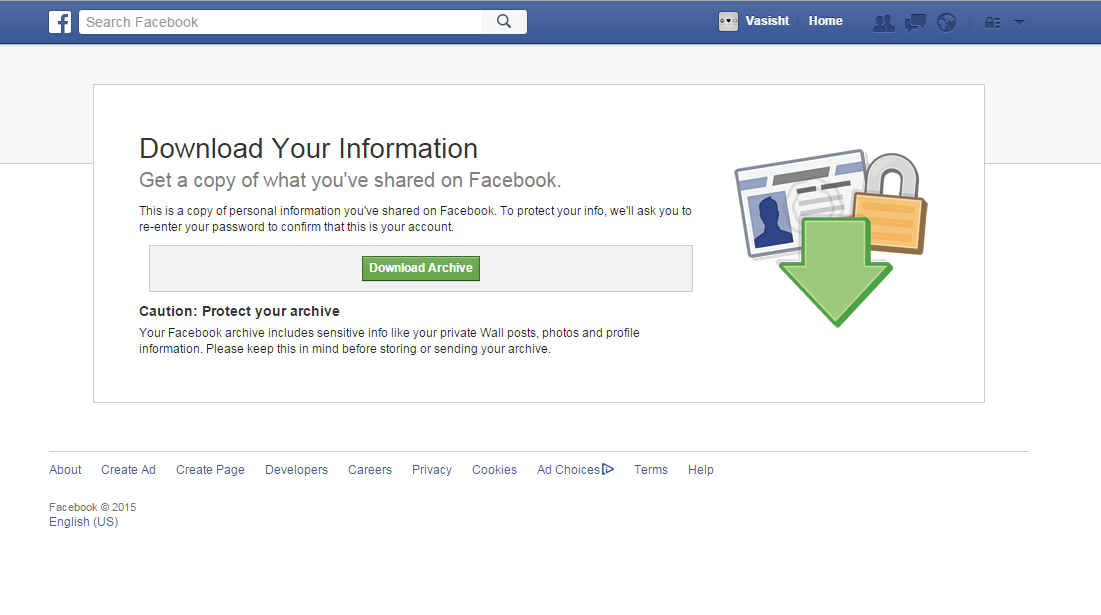
219How ToHow To Take Backup Of Your Facebook Profile
You might wonder how to download your photos, videos and messages from Facebook, but you don’t need to. Facebook has introduced a...
-

 280Data Security
280Data SecurityHackers Can Replace Apps on Your Android Device with New Vulnerability
The Zero-day vulnerability presented by IBM’s researchers Or Peles and Roee Hay will affect all Android devices. The two researchers from IBM’s...
-

 317Data Security
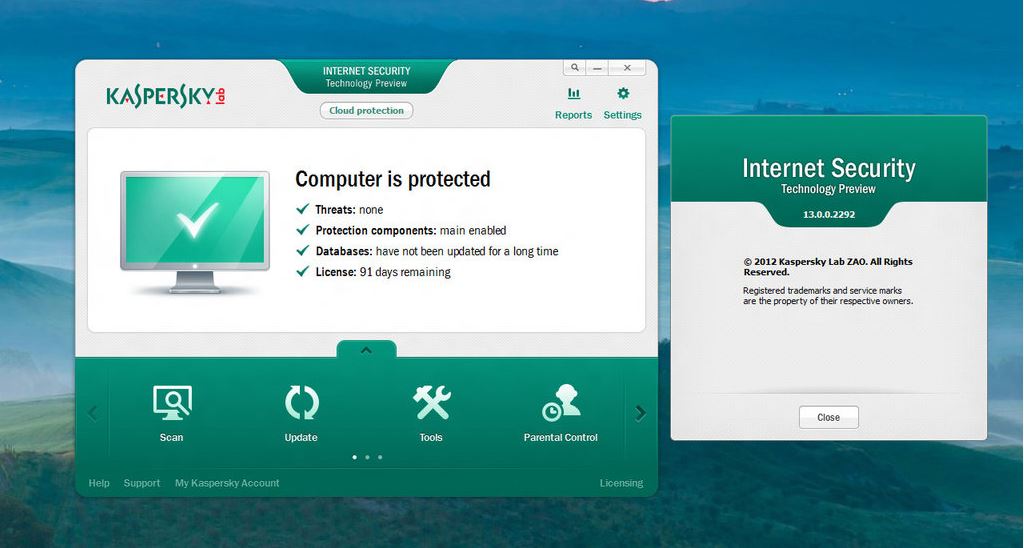
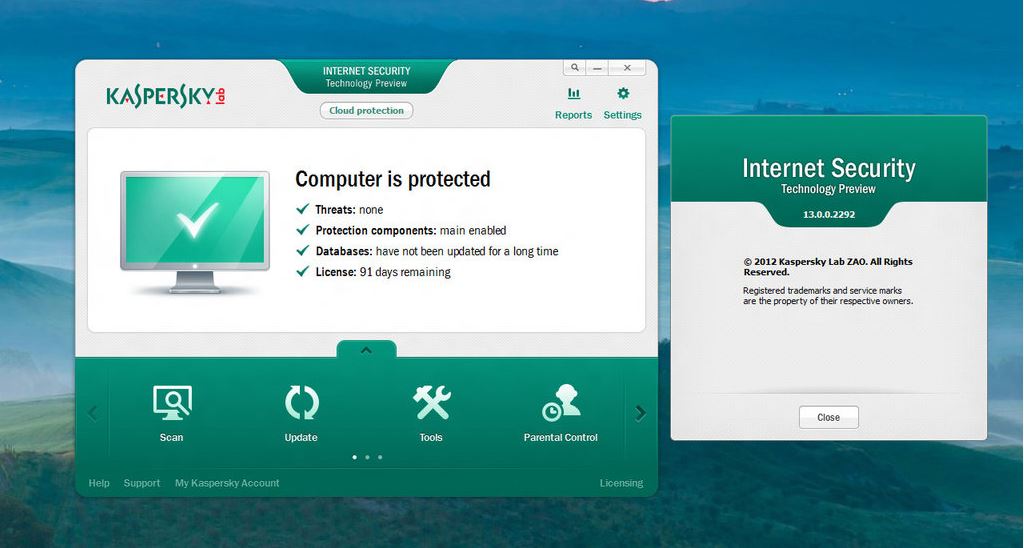
317Data SecurityKaspersky Accused of Producing Fake Malware to Sabotage Competitors
Reportedly, Kaspersky has been accused of making malware for more than ten years — The firm tricked other antiviruses into labeling it...
-

 317News
317NewsWindows 10 – Most Important Features you need to know
With Windows 10, Microsoft is making a strong step towards its goal of One Microsoft by looking forward to connect all the...
-

 232News
232NewsAzerbaijan Embassy to Russia Website Hacked With an Anti-War Message
A hacker going with the handle of Mr.H4rD3n hacked and defaced the official website of Embassy of Azerbaijan to Russia Thursday morning. The hacker...
-

 294Data Security
294Data SecurityHackers Can Disable House Arrest Ankle Bracelet without Raising Alert
Another blow to the law enforcement agencies – researcher from leading security group hacks his way out of ankle bracelet without raising...
-
 202Hacked
202HackedKaspersky Antivirus Made Fake Malware for More Than 10 Years – Ex-employees
Short Bytes: Two former employees of the security firm Kaspersky labs have told Reuters that the Russian company made fake malware for...
-

 133Opinion
133OpinionAre you still vulnerable to Stagefright? Get your Android device checked now
Security researchers found a vulnerability in Android that could allow attackers to steal information from smartphones through remotely executed code via a...
-
 170Secure Coding
170Secure CodingBuilding your own Web Crawler
Web crawler is a program that browses the Internet (World Wide Web) in a predetermined, configurable and automated manner and performs given...
-

 309News
309NewsThis Aerial Assault Drone Can Hack Computers Inside Walled Compounds
A drone is known for killing people or for its surveillance capabilities, but an aerial assault drone with hacking capabilities? Yes, you read that...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




