Search results for "Hidden"
-

 3.3KMalware
3.3KMalwareMalicious Google Ads Pushing Fake IP Scanner Software with Hidden Backdoor
A new Google malvertising campaign is leveraging a cluster of domains mimicking a legitimate IP scanner software to deliver a previously unknown...
-

 3.3KVulnerabilities
3.3KVulnerabilitiesWebinar: Learn How to Stop Hackers from Exploiting Hidden Identity Weaknesses
We all know passwords and firewalls are important, but what about the invisible threats lurking beneath the surface of your systems? Identity...
-

 4.2KMalware
4.2KMalwareExperts Warn of macOS Backdoor Hidden in Pirated Versions of Popular Software
Pirated applications targeting Apple macOS users have been observed containing a backdoor capable of granting attackers remote control to infected machines. “These...
-

 3.4KMalware
3.4KMalwareResearchers Unmask Sandman APT’s Hidden Link to China-Based KEYPLUG Backdoor
Tactical and targeting overlaps have been discovered between the enigmatic advanced persistent threat (APT) called Sandman and a China-based threat cluster that’s...
-
 668Malware
668MalwareMillions Infected by Spyware Hidden in Fake Telegram Apps on Google Play
Spyware masquerading as modified versions of Telegram have been spotted in the Google Play Store that’s designed to harvest sensitive information from...
-

 4.3KMalware
4.3KMalwareThe Hidden Dangers of Public Wi-Fi
Public Wi-Fi, which has long since become the norm, poses threats to not only individual users but also businesses. With the rise...
-

 2.0KMalware
2.0KMalwareHackers Deliver HotRat as Hidden Scripts in cracked software
The use of illegal software has been under circulation ever since there have been torrents and cracked software. Recent reports show that...
-

 1.2KData Breach
1.2KData BreachNew Cyber Platform Lab 1 Decodes Dark Web Data to Uncover Hidden Supply Chain Breaches
2022 was the year when inflation hit world economies, except in one corner of the global marketplace – stolen data. Ransomware payments...
-
 4.3KMalware
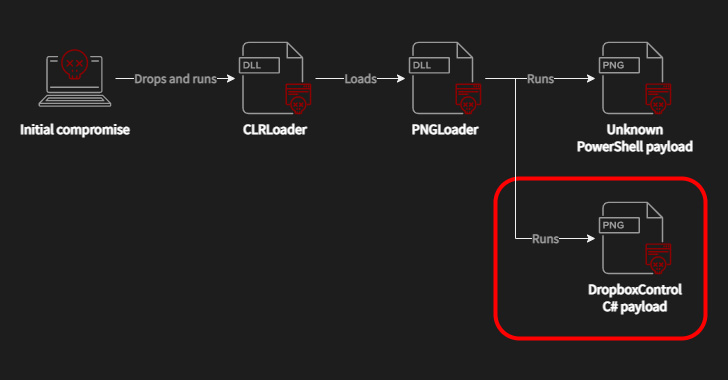
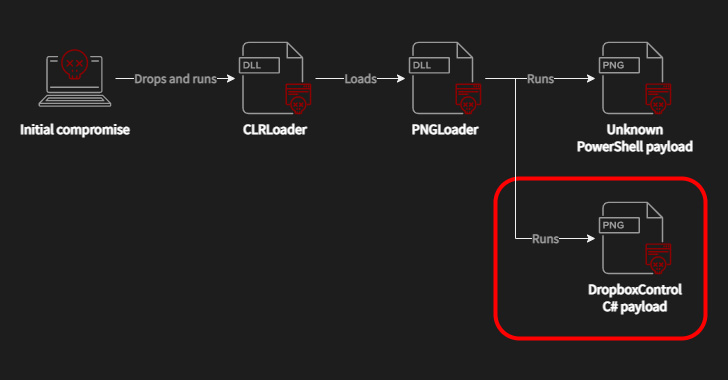
4.3KMalwareWorok Hackers Abuse Dropbox API to Exfiltrate Data via Backdoor Hidden in Images
A recently discovered cyber espionage group dubbed Worok has been found hiding malware in seemingly innocuous image files, corroborating a crucial link...
-

 1.4KPrivacy
1.4KPrivacyThe spy who rented to me? Throwing the spotlight on hidden cameras in Airbnbs
Do you find reports of spy cams found in vacation rentals unsettling? Try these tips for spotting hidden cameras to put your...
-

 4.6KMalware
4.6KMalwareChinese Hackers Distributing SMS Bomber Tool with Malware Hidden Inside
A threat cluster with ties to a hacking group called Tropic Trooper has been spotted using a previously undocumented malware coded in...
-

 2.9KMalware
2.9KMalwareSharkBot Banking Trojan Resurfaces On Google Play Store Hidden Behind 7 New Apps
As many as seven malicious Android apps discovered on the Google Play Store masqueraded as antivirus solutions to deploy a banking trojan...
-

 2.8KCyber Crime
2.8KCyber CrimeHidden in plain sight: How the dark web is spilling onto social media
A trip into the dark corners of Telegram, which has become a magnet for criminals peddling everything from illegal drugs to fake...
-
 1.2KCyber Crime
1.2KCyber CrimeCouple sold nuclear warship data hidden in peanut butter sandwich
The former Navy Nuclear engineer and his wife used a bubble gum package and peanut butter sandwich to hide SD card with...
-
 3.3KHow To
3.3KHow ToTop 3 Ways to Find a Hidden File on a Mac
Mac computers often have hidden files that you can’t see. Find out the practical ways to find and view the articles with...
-

 2.1KSurveillance
2.1KSurveillanceWhitehat hacker shows how to detect hidden cameras in Airbnb, hotels
The Whitehat hacker and IT security researcher Marcus Hutchins, who saved the world from the WannaCry ransomware attack, has shared simple yet...
-

 3.6KMalware
3.6KMalwareOusaban: Private photo collection hidden in a CABinet
Another in our occasional series demystifying Latin American banking trojans
-

 3.9KTutorials
3.9KTutorialsHOW TO DETECT HIDDEN CAMERAS OR SPY CAM IN A ROOM
Many users ignore it, but by using their laptop camera or any other camera with a WiFi connection, their MAC address will...
-
 2.0KMalware
2.0KMalwareDigging up InvisiMole’s hidden arsenal
ESET researchers reveal the modus operandi of the elusive InvisiMole group, including newly discovered ties with the Gamaredon group
-
 4.0KHack Tools
4.0KHack ToolsSharpHide – Tool To Create Hidden Registry Keys
Just a nice persistence trick to confuse DFIR investigation. Uses NtSetValueKey native API to create a hidden (null terminated) registry key. This...
-

 2.1KHow To
2.1KHow ToHow To View Hidden Files On MacOS Using Simple Steps?
It’s not just you, we all want to know why the Mac system takes up so much of space. I am curious...






